Hardening Hybrid Infrastructure
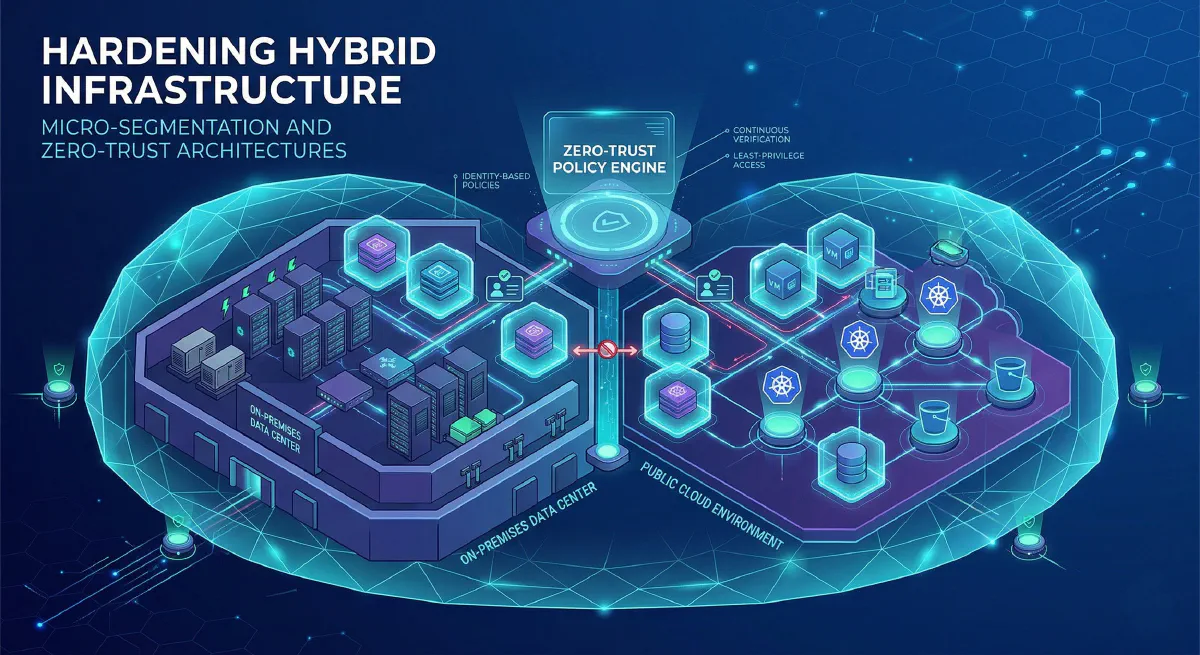
As organizations race to embrace the flexibility and scalability of hybrid cloud environments, they face a daunting security reality. The traditional security model, built around a porous network perimeter-the classic “castle-and-moat” strategy-is collapsing. Hybrid infrastructure, by definition, dissolves that moat, connecting on-premises data centers directly to multiple public clouds, SaaS applications, and a distributed workforce.
This new architecture offers incredible business agility but introduces complex security friction. The attack surface has expanded exponentially. Visibility is fractured across dynamic, heterogeneous environments. Attackers who gain a foothold “inside” the network find a flat landscape where they can move laterally, nearly undetected, toward their highest-value targets.
Hardening this fragmented infrastructure requires a fundamental shift in strategy. It demands a cellular defense model that moves protection from the network edge to the workload itself. The dynamic duo of this modern defense is Micro-Segmentation and Zero-Trust Architectures.
The Invisible Threat: Flat Networks and Lateral Movement
In a traditional, relatively flat network, security is concentrated at the perimeter. Once a user or application is authenticated-perhaps via VPN-they are considered “trusted” and granted broad access to the internal environment.
This implicit trust is the modern attacker’s greatest asset. They rarely breach the final target directly. Instead, they exploit a weak link-a phished credential, a vulnerable application tier, or a misconfigured development server-to establish an initial foothold. From this “island,” they use the unsegmented internal network to “hop” from server to server (lateral movement) until they find regulated data or critical systems, often months after the initial breach.
Micro-Segmentation and Zero Trust are specifically engineered to stop this “east-west” movement.
Strategic Pillar 1: Micro-Segmentation (The Tactical Cellular Defense)
Micro-Segmentation is a security method of logically dividing your hybrid environment into smaller, isolated secure zones, each with its own specific security controls and policies.
Instead of broad zones (like a DMZ or a internal network), micro-segmentation applies granular controls at the workload, application, tier, process, or even process level. It converts the data center from an open, vulnerable landscape into a series of highly secure cells.
The Key Benefits for Hybrid Hardening:
| Benefit | How it Hardens Hybrid Infrastructure |
|---|---|
| Containers Lateral Movement | Strictly controls traffic between workloads (east-west traffic). Even if one cell is compromised, the attacker is trapped, unable to “hop” to adjacent servers or services. |
| — | — |
| Reduces Blast Radius | A breach is contained within a singular, tiny micro-segment. The potential damage is minimized, and the scope of a containment and remediation effort is drastically reduced. |
| — | — |
| Simplifies Compliance | Regulations like PCI-DSS, HIPAA, and GDPR require proving who can access regulated data. Micro-Segmentation provides precise communication maps and audit trails, making continuous compliance demonstrably easier. |
| — | — |
| Unifies Visibility | A true micro-segmentation solution provides a single pane of glass to visualize all traffic flows-on-prem, across multiple clouds, and between endpoints-coupled with deep workload context. |
| — | — |
Strategic Pillar 2: Zero-Trust Architectures (The Foundational Strategy)
While Micro-Segmentation is a technical control, Zero-Trust is a comprehensive strategic framework. Its foundational philosophy can be summarized in one sentence: “Never Trust, Always Verify.”
Zero Trust completely eliminates the concept of default or implicit trust. It operates on three main non-negotiable principles:
- Strict Least-Privilege Access: Users, devices, applications, and processes are granted the bare minimum access needed to perform their job-nothing more. It reduces the attack surface by ensuring that even phished credentials grant a limited blast radius.
- Verify Continuously: Beyond an initial login, trust is continuously evaluated on a per-session basis, analyzing context such as user identity, device health, request location, and behavioral risk. Conditional access policies might require additional MFA or block access entirely if anomalies are detected.
- Assume Breach: Design controls under the assumption that an attacker has already bypassed the perimeter and is “inside.” This mindset shifts the focus from purely on perimeter prevention to internal detection, containment, and rapid response to lateral threats.
The Synergy: Strategy meets Tactics
It is crucial to understand that Zero Trust is the architecture, and Micro-Segmentation is one of its primary operational tools. One provides the “why” and the “what,” and the other provides the “how.”
A successful ZTA project in a hybrid environment rarely stalls on technology; it stalls when the underlying policy picture is missing.
- Zero Trust provides the decision framework: It dictates that “Sales Representative A using a healthy corporate laptop from the headquarters should have access to the Sales CRM, but not the HR database or the code repository.”
- Micro-Segmentation provides the granular enforcement: It translates that business intent into workload-specific network rules. It sandboxes the Sales CRM to ensure it only talks to the backend database and not to other applications on the same network subnet. It strictly enforces the isolation of non-production environments (development, testing) from production data.
By grounding your segmentation in Zero Trust principles of identity, context, and risk, you move beyond simple decentralized network perimeters to distributed, software-defined cellular defense.
Implementation Guide: A Phased, Policy-Cohesive Approach
Integrating micro-segmentation and zero-trust into a dynamic, heterogeneous hybrid setting is a journey, not a singular project. To avoid stalling in “pilot purgatory,” follow this strategic blueprint:
1. Shift Left on Visibility: Map Flows and Dependencies
The first step is visibility. You must know who is accessing what, where your critical protect surfaces are, and how data moves within your environment.
- Execute Asset Discovery: Build a complete inventory of all workloads, applications, data repositories, and user/service accounts across all platforms.
- Visualize Traffic Paths: Map the actual traffic flows between systems. Involve multiple cross-functional teams (security, networking, application owners) to ensure dependencies are understood before policies are written.
- Create an Application Baseline: Understand what “normal” traffic looks like to pinpoint risky anomalies and define accurate policies.
2. Plan a Cellular Architecture
Based on your visibility data, design your cellular defense.
- Define Protect Surfaces: Concentrates your controls on high-value targets. Map regulatory scope for compliance focus.
- Determine Boundaries: Create clear segmentation between environment types (e.g., prod vs. non-prod) and location types (on-prem, specific cloud regions, partner segments). Explicitly specify tier-to-tier and workload-to-workload flows (e.g., Web tier can only talk to App tier).
3. Codify Zero Trust Policies
Move away from static network constructs (IP addresses and ports) and adopt identity-based, dynamic policies that scale.
- Apply Explicit Verification: Always authenticate and authorize based on all available data points (identity, device posture, location, data classification).
- Define Least-Privilege Rules: Create policies that default to least privilege, granting the bare minimum access and auditing/denying everything else.
- Utilize Context and Attributes: Express policies using flexible labels or attributes (e.g., env=prod, app=hrm) rather than static constructs. Changes to the infrastructure can trigger automatic real-time policy updates.
4. Phase the Rollout
Do not attempt a “big bang” implementation across the entire enterprise.
- Pilot in non-production: Start in non-critical environments to test and refine policies.
- Simulate before enforcement: Validate the accuracy of your segmentation policies against historical and live traffic before they go live. This prevents outages during rollout.
- Document Rollback: Prioritize a straightforward exception process and rollback documented steps for when adjustments are needed.
5. Continuous Monitoring and Assurance
Hardening is not a “set it and forget it” activity. Modern architectures change rapidly.
- Real-time Visibility: Continuously analyze all traffic cross-environment and between segments for potential threats and anomalies.
- Continuous Improvement: Review latency and policy effectiveness regularly. Treat your segmentation and zero-trust policies as living documents that must adapt to new threats, organizational changes, and business growth (e.g., IoT adoption or cloud migration).
Conclusion
Hardening hybrid infrastructure is no longer an optional project; it is a strategic mandate for digital business resilience. Relying on perimeter defense in a world without perimeters is a failed strategy that hands the advantage to attackers.
By combining the declarative power of Zero-Trust Architectures (“never trust, always verify”) with the tactical cellular defense of Micro-Segmentation, you fundamentally transform your security posture. You move from a porous wall to a resilient cellular structure where unauthorized lateral movement is engineered to be impossible by design. You slashes attack impact, simplify complex compliance, and empower your organization to build unified access control that scales with confidence across every platform.