From Buzzword to Blueprint: Operationalizing Zero-Trust Across On-Premise and Multi-Cloud Environments
For years, Zero-Trust Architecture (ZTA) has dominated cybersecurity marketing. We all know the mantra: “Never Trust, Always Verify.”
But knowing the mantra and operating the machinery are two very different things.
The reality for most enterprises is a messy, hybrid existence. You have legacy, mission-critical applications running on-premise in a “castle-and-moat” configuration, sitting alongside dynamic Kubernetes clusters in AWS, serverless functions in Azure, and SaaS workloads like Microsoft 365.
The traditional perimeter is not just dissolving; it’s entirely irrelevant. Attackers are not blowing up the walls; they are using compromised credentials to walk through the front door and move laterally unhindered.
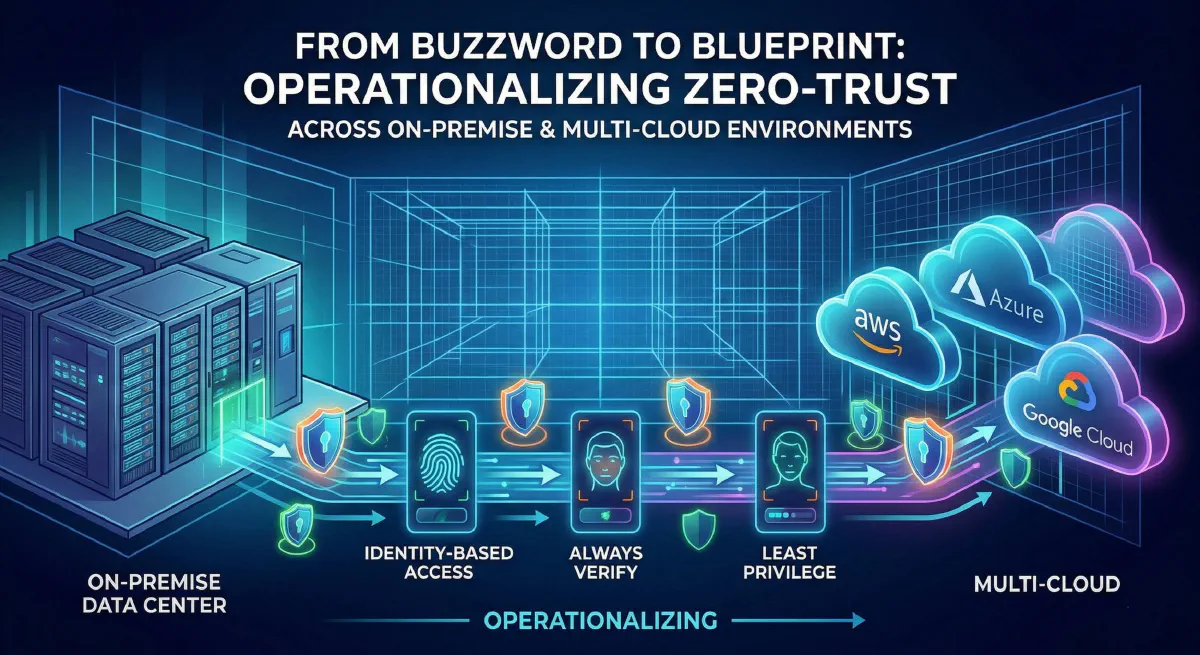
Operationalizing Zero-Trust—moving it from a slideshow concept to real-world enforcement—requires moving beyond network segmentation to a unified control plane based on identity, context, and continuous policy enforcement.
Here is a strategic blueprint for operationalizing ZTA across your on-premise and multi-cloud infrastructure.
Defining “Operational” Zero-Trust (The NIST Framework)
When we talk about operationalizing ZTA, we are moving from concept to the logical components defined in NIST SP 800-207. Your objective is to build a robust Control Plane that dictates interactions on the Data Plane.
To make Zero-Trust operational, you must implement three logical components above your silos:
- Policy Engine (PE): The brain. It ingests enterprise telemetry (SIEM, IDP, CDM) to make ultimate decisions to grant, deny, or revoke access to a resource based on real-time risk.
- Policy Administrator (PA): The action arm. It executes the decision of the PE. It communicates with the Policy Enforcement Points to establish (or terminate) communication channels.
- Policy Enforcement Point (PEP): The gatekeeper. A software component (like an agent, proxy, or API gateway) that strictly enables and monitors authorized connections between a subject and a resource.
Your architecture must move away from static, network-based silos to dynamic, identity-centric decision-making using these components.
Pillar 1: The New Control Plane – Identity & Workload Access (IAM)
Identity is the foundation of operational Zero-Trust. In a hybrid environment, “Identity” must expand beyond human users to include Machine Identities (services, APIs, devices, and containers).
Operational Move: Centralize and Federate
You cannot have isolated identity silos for on-premise AD, AWS IAM, Azure AD, and GCP IAM. Attacks thrive in the gaps between these systems.
- Federate Identity: Use modern protocols (SAML 2.0, OIDC) to federate all cloud providers and SaaS apps to a single, authoritative Identity Provider (IdP). This is your strategic source of truth.
- Implement Adaptive Multi-Factor Authentication (MFA): “Standard” MFA is reactive. Operational Zero-Trust requires adaptive, context-aware MFA. Your Policy Engine must evaluate context every time MFA is requested:
- User identity/role: (Are they in the Admin group?)
- Device health/posture: (Is the device managed, encrypted, and compliant?)
- Geolocation/IP reputation: (Are they logging in from an unknown city?)
- Time of day/behavioral risk: (Is a developer accessing a database at 2 AM?)
If the risk score is too high, the IdP must automatically step up authentication (request additional factors) or block the request entirely before access is granted.
Pillar 2: The Action Arm – Micro-Segmentation and Service Mesh
Traditional, flat networks allow for catastrophic lateral movement. Operationalizing Zero-Trust requires dividing your network—on-premise and across multiple clouds—into smaller, isolated secure cells (micro-segments).
Operational Move: Identity-Based Enforcement
Segmentation must move beyond blast-radius network constructs (IP addresses and ports) to adopt identity-based, dynamic policies that scale.
On-Premise/Data Center: Micro-Segmentation
- Software-Defined Perimeter (SDP): Implement agents or sidecar proxies at the workload, process, or application level. SDP solutions enforce “Least Privilege” access, effectively sandboxing every workload. A compromised web server in your data center should engineered to be impossible to talk east-west to an adjacent application server on the same network subnet unless explicitly authorized.
Cloud-Native/Multi-Cloud: Service Mesh and CNI
- Kubernetes Service Mesh (e.g., Istio, Linkerd): Multi-cloud applications running on K8s must implement a service mesh to handle service-to-service authentication, authorization, and encryption (mTLS).
- Identity infrastructures (e.g., SPIFFE/SPIRE): Multi-cloud applications rely on service authentication. Use workload identity tools to automatically issue short-lived, verifiable X.509 certificates for authentication between services (mTLS), regardless of whether they are running in AWS or GCP. This allows your security to be based on identity, not fragmented cloud-specific network settings.
Pillar 3: The Feedback Loop – Visibility, Analytics, & Automation
Zero Trust is a continuous loop. You must prove the artifact is what we expect continuously. This requires Ubiquitous visibility and automated response.
Operational Move: Context-Aware Detection (The SIEM/XDR Link)
You cannot manage what you cannot see. Your Policy Engine needs telemetry from the SIEM, IDP, and EDR to make intelligent access decisions.
Operational Workflow:
- A SOAR playbook identifies a workstation with suspicious ransomware behavior (detected by EDR).
- It instantly updates the central user context database (CDM) within the central IdP.
- The central IdP/PE immediately revokes the active session token and suspends the user’s account across all connected multi-cloud environments (AWS, Azure, SaaS), trapping the threat within a single, tiny micro-segment boundary.
This transformation from reactive detection to proactive response mitigates attack impact and reduce complex compliance friction.
Phased Implementation Roadmap (Don’t Boil the Ocean)
Operationalizing Zero-Trust is a journey, not a singular project. To avoid pilot purgatory, plan your architecture strategically:
Step 1: Discover & Baseline (Identify Protect Surfaces)
- Define all users, devices, services, and SaaS applications. Do not rely on native cloud silos for inventory.
- Identify high-value targets (protect surfaces) and critical dependencies.
- Visualize traffic flows. Document standard user behavior for later behavioral baselining.
Step 2: Implement Conditional Access (Preparation/Preparation)
- Centralize and federate your IdP. Build the standardized data baseline.
- Deploy mTLS and workload identity for multi-cloud application access.
- Create adaptive, context-aware conditional access policies (Adaptive MFA).
Step 3: Enforce Segmentation (Short-Term Triage/Preparation)
- Start segmentation in high-frequency, well-understood scenarios. Focus on high-value data and non-production boundaries.
- Validate and simulate policies using live traffic data before going to full enforcement. This prevents outages during rollout.
Step 4: Automate Response & Validate Continuously (Containment/Preparation)
- Integrate IdP, EDR, and SOAR for automated threat response.
- Update playbooks to utilize context and dynamic attributes (e.g., automatically block IPs or disable accounts based on risk scores).
- Schedule a formal post-incident review and continuously update playbooks to feed lessons learned back into the pipeline.
Conclusion
Operationalizing Zero-Trust across on-premise and multi-cloud environments requires unifying the declarative simplicity of Zero Trust principles with standard governance and continuous, automated enforcement. Relying on disconnected native cloud tools for compliance will always lead to gaps, friction, and reactive defense. By aligning ZTA’s strategic principles phase by phase and leveraging a cohesive SIEM/SOAR/IdP stack, you build an architecture that is simultaneously high-security, efficient, and auditable—a cohesive strategy where engineering an vulnerable state is engineered to be impossible by design.