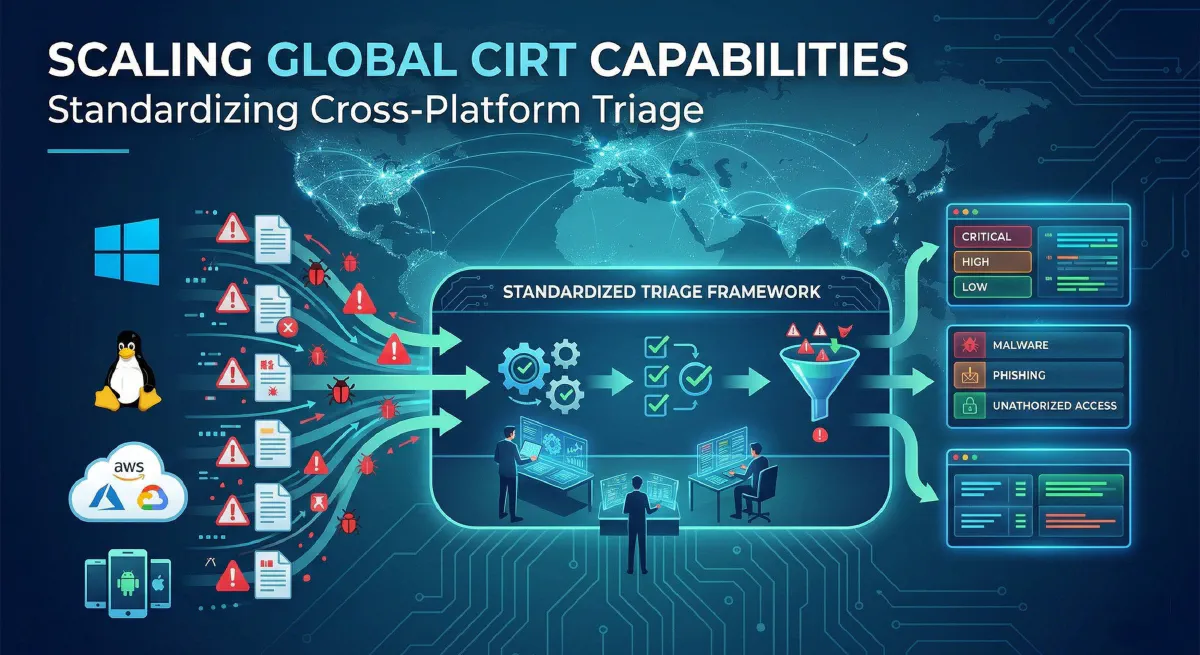
Scaling Global CIRT Capabilities: Standardizing Cross-Platform Triage
Twenty years in the information security trenches will teach you a lot of hard lessons, but perhaps the most undeniable is this: Threat actors do not respect your infrastructure boundaries.
They don’t care that your Windows fleet is guarded by a best-in-class EDR, while your containerized Linux workloads rely on legacy monitoring, and your multi-cloud environments (AWS, Azure, GCP) are governed by fragmented security configurations. In fact, they thrive in the seams of your visibility.
As we push deeper into 2026, the technological landscape has never been more fractured. For global Cyber Incident Response Teams (CIRTs), the traditional approach to incident triage—managing a dozen different consoles, custom bash/PowerShell scripts, and platform-specific playbooks—is no longer just inefficient; it is an existential risk to the business. To survive, modern CIRTs must evolve from reactive firefighting to building a highly scalable, standardized, cross-platform triage architecture.
Here is how elite security engineering teams are solving the triage fragmentation problem at a global scale.
The Fragmentation Problem: Cognitive Load and MTTR
In a classic enterprise environment, a single supply-chain compromise might trigger alerts across a developer’s macOS laptop, a Windows Active Directory domain controller, and a Kubernetes cluster hosted in AWS.
If your CIRT relies on platform-specific triage, your response looks something like this:
- macOS: An analyst pulls unified logs and examines
LaunchDaemons. - Windows: Another analyst uses EDR live response to pull MFTs and registry hives.
- Linux/K8s: Cloud engineers are paged to pull
auditdlogs and AWS CloudTrail telemetry.
This disjointed approach skyrockets your Mean Time To Respond (MTTR). Analysts suffer from extreme cognitive load, forced to mentally translate artifacts between completely different operating system paradigms. Furthermore, relying heavily on tribal knowledge for specific OS intricacies means your team cannot scale globally. You cannot staff Level 3 experts for every single platform in every single time zone.
The solution is abstraction.
The Core Pillars of Standardized Triage
To scale global CIRT capabilities, organizations must abstract the underlying operating system and cloud environment away from the analyst during the initial triage phase.
1. Unified Telemetry and Abstraction Layers
The first step to standardization is adopting an abstraction layer for your endpoint queries. Tools like OSQuery, Velociraptor, or GRR Rapid Response have become the gold standard for cross-platform DFIR (Digital Forensics and Incident Response).
Instead of an analyst writing three different scripts to hunt for persistence mechanisms, they execute a single, abstracted query.
For example, an artifact conceptually named Hunt.MaliciousPersistence handles the translation under the hood:
- If Windows: Queries Run Keys, Services, Scheduled Tasks, WMI event consumers.
- If Linux: Queries cron jobs, systemd services,
rc.local. - If macOS: Queries
LaunchAgents,LaunchDaemons, login items.
This allows a Tier 1 or Tier 2 analyst in any region to confidently pull actionable forensics without needing to be an expert in the underlying kernel architecture.
2. Data Normalization and the OCSF
Pulling the data is only half the battle; reading it is the other. In 2026, relying on proprietary log formats is a losing game. Global CIRTs are increasingly standardizing their SIEM and data lake ingest pipelines using the Open Cybersecurity Schema Framework (OCSF).
By normalizing cross-platform triage data into a unified schema, your detection engineering and incident response teams speak the exact same language. A process execution event looks the same whether it originated from an EDR agent on Windows or a CloudTrail log monitoring an ECS container.
3. AI-Driven Automation and SOAR Integration
Triage is not simply data collection; it is the rapid analysis of that data to reach a verdict. Modern multi-cloud environments generate far too much noise for humans to manually filter.
By integrating your standardized triage framework with your SOAR (Security Orchestration, Automation, and Response) platform, you can orchestrate immediate, platform-agnostic collection the moment a high-fidelity alert fires. In 2025 and 2026, we have seen a massive leap in AI-enabled triage filtering.
When your SOAR pulls the abstracted artifacts, an integrated LLM/AI pipeline can pre-process the triage package:
- Correlating parent-child process anomalies.
- Checking file hashes against threat intelligence feeds.
- Highlighting anomalous command-line arguments.
- Presenting the human analyst with a summarized context brief and a confidence score.
The Goal: By the time the CIRT analyst opens the ticket, the cross-platform triage is already complete, the data is normalized, and the AI has highlighted the critical anomalies. The analyst is making a decision, not conducting data entry.
Building the Architecture: A Strategic Blueprint
For Technical Leaders and CISOs looking to implement this within their own global CIRTs, here is a phased approach to modernization:
Phase I: Audit and Consolidate
Identify every tool currently used for endpoint and cloud triage. Map out the blind spots. If your XDR solution claims to be cross-platform but drops coverage on legacy Linux or heavily restricted macOS systems, you need a supplementary open-source DFIR framework (like Velociraptor) deployed alongside it to close the gap.
Phase II: Build the Universal Artifact Library
Task your Senior Incident Handlers and Detection Engineers with building a repository of platform-agnostic triage queries. Categorize them by the MITRE ATT&CK® tactics: Initial Access, Persistence, Privilege Escalation, Credential Access, etc. Ensure these queries return structured, machine-readable data (JSON/YAML) rather than flat text.
Phase III: Automate the First 15 Minutes
Hook your Universal Artifact Library into your SOAR platform. Configure playbooks so that when an alert is escalated, the SOAR automatically executes the appropriate artifact collection across all involved assets, regardless of their OS.
Phase IV: Feedback Loops and Threat Intel
A standardized architecture allows for rapid threat hunting. When a new Zero-Day drops or a novel threat intelligence indicator is shared by CISA, your CIRT shouldn’t be scrambling to figure out how to search for it across 5 different platforms. They update the universal query, push it globally, and hunt across the entire enterprise in minutes.
Conclusion
The mark of a mature, globally scalable CIRT is not the number of highly specialized ninja-level analysts it employs, but the efficiency and standardization of its systems. Technology moves too fast, and adversaries are too well-funded for us to rely on artisanal, hand-crafted incident response procedures.
Standardizing cross-platform triage empowers your team to cut through the multi-cloud noise, drastically reduce MTTR, and focus human intellect where it belongs: outsmarting the adversary. In 2026, agility is your greatest weapon. Make sure your architecture allows you to wield it.
About the Author Sam Jobes, CISA-CISSP, is a 20-year information security veteran specializing in enterprise security architecture, GRC automation, and building scalable infosec programs for high-growth technology companies.