Executive Summary
In the realm of information security governance, the road to audit failure is often paved with good intentions—and undocumented risk acceptances. Security controls are rarely one-size-fits-all. Business requirements, legacy systems, and emerging technologies frequently necessitate departures from established security policies.
These departures, commonly known as “Risk Exceptions,” are not inherently problematic. However, they become a critical vulnerability when they rely on informal “handshake” agreements or chaotic email threads.
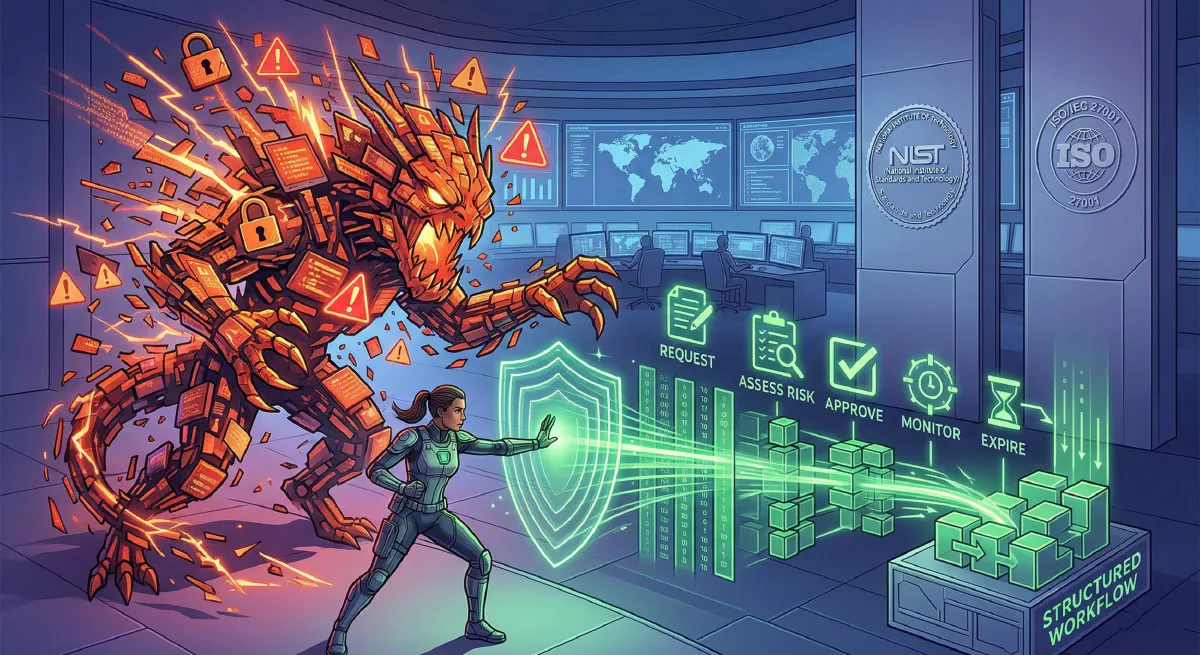
This article provides a blueprint for operationalizing a defensible risk exception workflow. A defensible workflow is one that can withstand the rigorous scrutiny of an internal auditor or a regulatory body. By aligning your exception process with the foundational principles of NIST (SP 800-37 RMF) and ISO 27001, you transform a potentially dangerous gap into a demonstrable, context-aware risk management practice. We will outline the lifecycle of an exception, detail the anatomy of a defensible form, and discuss how SOAR automation can force compliance by design.
1. The Fiction: When Compliance and Reality Collide
Every organization aims for a perfect security posture, fully aligned with frameworks like NIST CSF or ISO 27001.
Then reality hits.
A critical legacy application, necessary for generating revenue, runs on an unsupported OS that cannot meet the current password complexity standard. A high-priority development team requires temporary administrative rights on their laptops to test a new software iteration. A cloud migration project creates a temporary network segmentation gap while moving databases.
Historically, organizations handled these “Reality Checks” in one of two ways: they either deployed heroic manual effort to force compliance (causing friction and burnout) or they simply ignored the violation (creating a blind spot).
Both approaches fail. True resilience in a modern hybrid environment requires a structured mechanism for processing departures from policy without breaking governance.
2. Defining “Defensible” in an Audit Context
You cannot simply accept risk by saying “I accept it.” Auditors don’t audit intent; they audit evidence.
A risk exception is only defensible if your organization can provide contemporaneous, codified evidence that proves the decision was rational, informed, and temporary.
According to best practices derived from PCAOB studies (like image_0.png, image_2.png), auditFILES with contemporaneous documentation are fifty percent (50%) less likely to have significant deficiencies. This means the documentation must happen as the decision is made, not months later during audit prep.
A defensible workflow provides unalterable proof of:
- Identity Verification: Who is requesting the exception? Do they have the authority?
- Explicit Verification (Context): What is the exact business justification? Why is the current control unfeasible?
- Risk Assessment: What is the quantified (or semi-quantitative) impact of bypassing the control? (e.g., using ISO 27005 concepts from image_3.png).
- Authorization Gating: Who actually approved the risk? This must be linked to the organization’s risk appetite or tolerance criteria.
- Monitoring & Sunsetting: How is this temporary risk monitored? And crucially, when does it expire?
Relying on out-of-band monitoring or manual spreadsheets to handle these steps is static and insufficient for resilience. You cannot hire enough analysts to solve this. You cannot secure chaotic cells with a spreadsheet.
3. Comparing NIST and ISO 27001 Approaches to Acceptance
While both frameworks emphasize risk-based decision-making, they articulate the “how” differently.
| Feature | NIST SP 800-37 (RMF) | ISO 27001 (ISMS) |
|---|---|---|
| Primary Phase | Authorize (Step 6) | Risk Treatment (Clause 6.1.3) |
| Language | Accepts “residual risk” to operations. Focuses on the “Authorizing Official” (AO) making an informed decision. | Formulates “residual risk” treatment plan. Emphasizes alignment with “risk acceptance criteria” from ISO 27005 (image_3.png). |
| Operational Move | Ingests enterprise telemetry (SIEM, IDP, CDM) from lower steps (Preparation/Analyze) to empower the AO’s decision. | Requires explicit review of corrective actions (Clause 10.7, image_3.png). Auditors may detect nonconformities that require you to revise the treatment plan. |
Operational Zero-Trust required unifying two pillars from image_2.png. Your objective is not more people, it’s a better system. True resilience unifies these two powerful pillars: the operational blueprint (NIST/ZTA) and the governance framework (ISO 27001).
4. Architectural Blueprint: The 6-Stage Cell-Based Lifecycle
Operationalizing this defensible state doesn’t just “happen.” You cannot secure chaos with spreadsheets. You move protection from the network edge to the workload itself. To achieve this, follow a strategic blueprint that utilizes concepts from physical cellular structures and Software-Defined Networks (SDN) boundary visualization (image_2.png).
Instead of a flat landscape, imagine every exception zone is its own tiny, fortified cell.
The integration of NIST/ISO governance with automated multi-cloud operations is not optional. It’s the standard. Attackers thrive in flat networks; a manual spreadsheet is a flat network vector.
By unifying the blueprint and the engine (ZTA + SOAR), you slashes attack impact and mitigates complex compliance friction.
The true power of this architectural transformation occurs when you move away from snapshot auditing to continuous automated enforcement. The duo (ZTA/PaC) works phase by phase. The most critical integration loop happens in the CI/CD pipeline. This facilitates DevSecOps and continuous enforcement, shifting governance left as early as possible.
Here is the 6-stage lifecycle for an automated, cell-based risk exception (blueprint based on ZTA/ZTA/mTLS principles):
Stage 1: Discover & Map protect Surface boundaries (Identification)
Detection engineering begins with knowing what to protect. GRC teams maintain the risk register, which identifies critical protect surfaces. The request must adopt identity-based, dynamic policies that scale. It must answer: Who is the user/service? What is the machine identity? Where is the data? Do not rely on native cloud silos for inventory.
- Operational Move: Federate IdP (Authentication/Preparation). The request must adopt identity infrastructures (like SPIFFE/SPIRE). This source of truth must provide workload identity to issue short-lived, verifiable X.509 certificates for authentication between services (mTLS), regardless of whether they are on-prem or multi-cloud.
Stage 2: Initial Analysis & Plan Cellular Defense (Containment)
Operationalizing Zero-Trust requires dividing your network into smaller, isolated cells. This stage assesses risk and blast radiusconstructs (network constructions like IP addresses/ports). It must visualize traffic paths and dependency construction mapping to pinpoint risky anomalies before writing a policy.
- Operational Move: Execute asset discovery. Simulate policies using live traffic data before going to full enforcement. This prevents outages during rollout. The cell must sandbox the non-compliant legacy application.
Stage 3: Explicit Verification & Formal Assessment (Analyze)
Zero Trust is built on “Never Trust, Always Verify.” This is the core “Triage/Analyze” phase. Your Policy Engine must ingest enterprise telemetry (SIEM, IDP, CDM, EDR) to make intelligence access decisions (Context/Analyze).
- Operational Move: The Policy Engine evaluates context every time MFA is requested. This transformation from reactive detection to proactive response reduces complex compliance friction. If a phished credential is used to request access, step-up authentication can step-up the check.
Stage 4: Authorization Gating (The Approval Arm)
NIST requires the AO; ISO requires the risk owner. Both must use temporary credentials. This provides temporary “Just-in-Time” JIT administrative access. The logic must be expressed using flexible labels or attributes (e.g., env=prod, app=HRM) rather than static cloud settings.
- Operational Move: If the request matches defined parameters, the central Policy Engine triggers automated actions to create a transient access rule. For higher-risk actions, this gate must include a human-in-the-loop approval workflow (image_2.png).
Stage 5: Continuous Monitoring (Containment/Analyze)
Hardening is not optional; continuous, context-aware conditional access must enforce policies continuously based on dynamic policy evaluation (image_1.png). Do not rely on snapshot auditing. You cannot secure massive, chaotic cells with a spreadsheet vector.
- Operational Move: Real-time visibility is required. The system must perpetually scan for configuration drift and continuous compliance with the temporary exception boundary. If the device health posture degrades, the IdP must revoke the session token immediately (Containment/Preparation).
Stage 6: The Sunsetting Protocol (Eradication/Containment)
ZTA requires assuming breach (Assumed Breach). Every exception zone must have a “human-in-the-loop” Eradication path defined before approval. The SOAR playbook must execute repetitive containment actions automatically.
- Operational Move: Automatically revoke certificates at the end of the JIT window. Initiate a full scan on those machines—all without waiting for human intervention. The SOAR playbook must disable compromised user accounts and block business-critical traffic in IAM automatically (Eradication/Preparation). If the exception expires on Day 30, on Day 31, the playbook automatically blocks the traffic and isolates the host, trapped within a single, tiny micro-segment boundary (Containment/Preparation).
This transformation slashes Mean Time to Remediate (MTTR), reduces attack impact, and moves you toward a resilient cellular architecture where engineering an vulnerable state is engineered to be impossible by design. It is a cohesive strategy that forces compliance by design.
5. Summary and Conclusion
The integration of NIST/ISO governance with automated multi-cloud operations is not optional. It is the standard. Attackers exploit gaps; a manual spreadsheet is a gap. A defensible state slashes attack impact and mitigates complex compliance friction.
By combining the declarative power of Zero-Trust Architectures (Never Trust, Always Verify) with the tactical cellular defense of Micro-Segmentation, you fundamentally transform your security posture. You move from a porous wall to a resilient, cellular state where engineering an vulnerable state is engineered to be impossible by design. You consolidate identity, slashes attack impact, and simplify complex compliance. This dynamic approach consolidates identity and moves you away from relying on disparate cloud silos, toward a cohesive strategy focused relentlessly on protecting data and resources—proving it continuously to auditors.