In my two decades navigating the ever-shifting landscape of information security, I have witnessed countless evolutions in our tools, tactics, and adversaries. Yet, one enduring paradox remains: Security Operations Centers (SOCs) have never had more data, and yet executive boards have never felt less secure.
We are drowning in technical telemetry—EDR alerts, firewall drop logs, vulnerability scanner outputs, and SIEM dashboards glowing with millions of “prevented attacks.” But when the Chief Information Security Officer (CISO) stands before the Audit Committee to present these numbers, the inevitable question from the board is simple: “Are we actually more secure today than we were yesterday?”
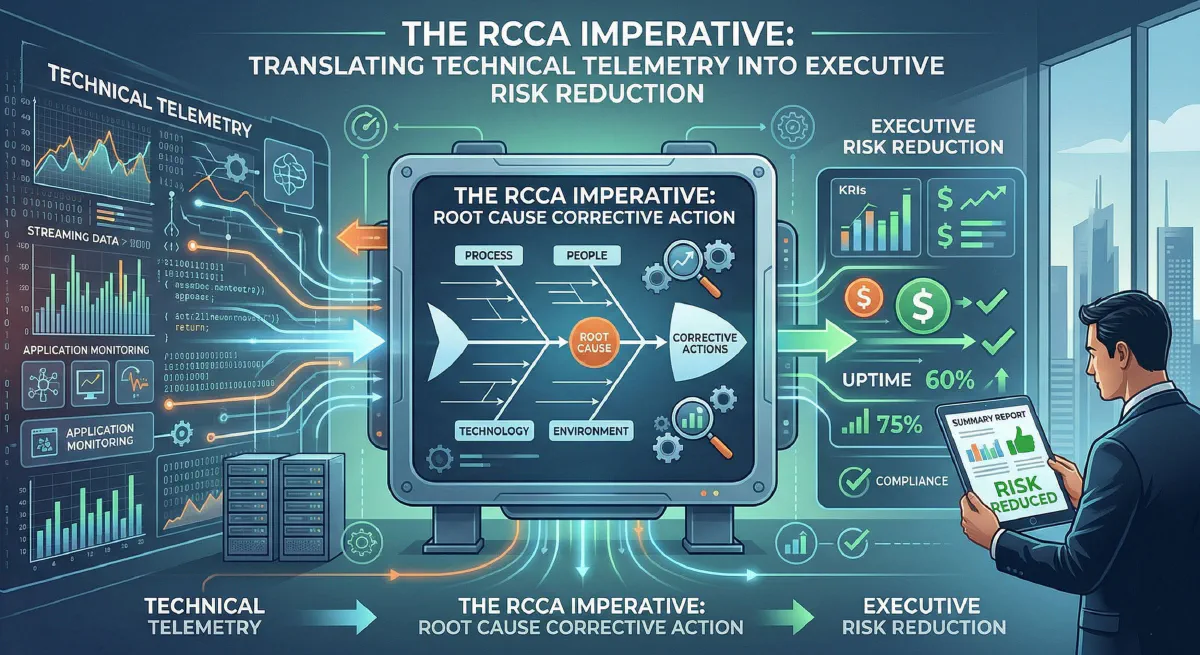
If your answer relies on the volume of blocked phishing emails or the number of patched CVEs, you are falling into the Telemetry Trap. To bridge the chasm between operational data and boardroom confidence, we must adopt a framework that translates reactive technical signals into proactive, systemic resilience.
Welcome to the RCCA Imperative.
The Telemetry Trap: Why Vanity Metrics Fail
In cybersecurity, we have a bad habit of reporting the weather instead of building better shelters.
When we tell an executive team that we blocked 5,000 malicious IPs this week, we are presenting a vanity metric. It sounds impressive, but it fails to articulate business impact. To an executive, high telemetry volume doesn’t signify a strong defense; it signifies a high-risk environment. It prompts the question: Why are we being attacked 5,000 times a week, and what happens when the 5,001st attempt gets through?
Telemetry tells us what happened. It rarely tells us why it happened, and it certainly doesn’t tell us how to systematically prevent it from happening again. This is where traditional Incident Response (IR) often falls short. Traditional IR is inherently cyclical: detect, contain, eradicate, recover. The analyst closes the ticket, and the SOC waits for the next alert. This whack-a-mole approach exhausts teams and burns capital without materially reducing the organization’s attack surface.
Decoding RCCA for Information Security
Root Cause Corrective Action (RCCA) is a methodology born in the rigorous environments of aerospace engineering and manufacturing quality control. Its premise is elegantly simple: do not just fix the symptom; relentlessly hunt down the systemic failure that allowed the symptom to exist, and implement a corrective action that guarantees it cannot happen again.
When adapted for information security, RCCA is the ultimate translation engine. It converts a technical alert into an executive risk reduction strategy.
In the context of modern cyber defense, RCCA requires a paradigm shift:
- Root Cause Analysis (RCA): Moving beyond the immediate technical exploit (e.g., “The attacker used a stolen session token”) to uncover the systemic control failure (e.g., “Our Identity and Access Management policy does not enforce continuous authentication or token expiration on unmanaged devices”).
- Corrective Action (CA): Moving beyond the immediate remediation (e.g., “Revoke the token and reset the password”) to implement an architectural or procedural fix (e.g., “Deploy conditional access policies requiring managed devices for critical applications”).
The Anatomy of a Cyber RCCA: The “Five Whys”
To illustrate the RCCA Imperative, let’s apply the classic “Five Whys” technique to a modern, highly relevant scenario: a cloud infrastructure compromise.
- The Telemetry (The Symptom): An XDR alert triggers for anomalous data exfiltration from an AWS S3 bucket.
- Why was data exfiltrated? An attacker assumed an IAM role with excessive read permissions.
- Why did the attacker have that IAM role? They compromised a developer’s CI/CD pipeline service account credential.
- Why was the service account credential compromised? It was hardcoded into a script pushed to a public GitHub repository.
- Why was it hardcoded? The development team bypassed the secrets management vault to meet a tight release deadline.
- Why were they able to bypass the vault without detection? (The True Root Cause): We lack automated pre-commit hooks for secret scanning, and our CI/CD pipeline does not fail builds that violate security gating.
Traditional IR stops at Step 2 (revoke the credential, delete the script). RCCA drives you to Step 5.
Translating Telemetry to Executive Risk Reduction
Once the root cause is identified, the next step is translating this narrative for the executive suite. Executives do not manage alerts; they manage risk, allocate budgets, and protect shareholder value.
Here is how the RCCA framework transforms the conversation from technical jargon to executive risk reduction:
| The Technical View (SOC) | The RCCA Translation (Architecture) | The Executive View (Boardroom) |
|---|---|---|
| Alert: EDR isolated a host executing a malicious macro. | Root Cause: Email gateway misconfiguration allowed macro-enabled documents from external senders. | Risk Identified: High probability of ransomware execution due to porous vendor communication channels. |
| Action: Host wiped, user password reset. | Corrective Action: Implement global Group Policy to disable internet-originated macros; route external docs through a sandboxing gateway. | Risk Reduction: Eliminated a primary vector for ransomware, reducing potential business downtime exposure by an estimated $2.5M. |
| Metric: Time-to-Contain (15 mins). | Metric: Security Control Coverage increased by 15%. | Metric: Systemic Recidivism Rate (prevented future occurrences of this specific root cause). |
Implementing the RCCA Imperative in Your Organization
Transitioning your security apparatus from an alert-driven model to an RCCA-driven model requires intentional leadership. Here are the core pillars to enact this change:
1. Institute the “Blameless Post-Mortem”
RCCA dies the moment it turns into a witch hunt. If developers or system administrators fear punishment for the root cause, they will obfuscate the truth. Security leaders must cultivate a culture where human error is viewed as a symptom of a poorly designed system. The goal is to fix the system, not fire the human.
2. Redefine Key Performance Indicators (KPIs)
Stop highlighting the volume of blocked attacks. Instead, report on Recidivism Rate (how often are we investigating incidents with the same root cause?) and Control Efficacy (how many incidents led to the implementation of an automated preventative control?). Reward your teams not just for putting out the fire, but for fireproofing the building.
3. Integrate Threat Intelligence with Enterprise Architecture
RCCA should create a continuous feedback loop. When the SOC identifies a root cause, that data must flow directly to the Enterprise Architecture team. Every incident must result in a hardening of the infrastructure. If your IR team and Architecture team do not have a weekly sync, your RCCA pipeline is broken.
4. Automate the Corrective Action
In 2026, relying on manual processes for corrective action is a vulnerability in itself. Once a corrective action is identified (e.g., enforcing MFA on a legacy app), use Infrastructure as Code (IaC) and policy engines to deploy and enforce the fix globally. Code ensures the corrective action doesn’t degrade over time.
Conclusion
As security professionals, our ultimate duty is not to comb through logs, but to build resilient organizations. The barrage of technical telemetry is only useful if it serves as a compass pointing toward structural weaknesses.
By embracing the RCCA Imperative, we elevate our discipline. We stop speaking to the business in the language of threats and alerts, and begin speaking in the language of systemic risk reduction and proactive architecture. It is time to stop counting the drops of rain, and start fixing the roof.
About the Author Sam Jobes, CISA-CISSP, is a 20-year information security veteran specializing in enterprise security architecture, GRC automation, and building scalable infosec programs for high-growth technology companies.