Accelerating Incident Response with SIEM and SOAR Automation
In the digital age, a cybersecurity breach isn’t just an IT issue; it’s a business-critical emergency. When an attacker is inside your network, every second counts. The longer they remain undetected, the greater the potential for data exfiltration, service disruption, and lasting reputational damage.
The primary metric of success for a Security Operations Center (SOC) is often Mean Time to Remediate (MTTR)-the average time it takes to neutralize a confirmed threat. Historically, MTTR has been measured in days or even weeks. In today’s fast-moving threat landscape, that is simply unacceptable.
The bottleneck isn’t the skill of security analysts; it’s the volume of data they are forced to process. Human teams are drowning in a sea of alerts, struggling with disconnected tools and slow, manual response procedures. To beat modern attackers, you must accelerate your response. The solution is the powerful integration of SIEM and SOAR automation.
The Bottleneck: Why Manual Incident Response Fails
To appreciate the solution, we must first understand the problem. A typical modern organization faces several critical challenges that slow down incident response:
- Alert Fatigue: Security tools generate thousands of alerts daily. Sifting through this noise to find genuine threats causes analyst burnout and leads to missed critical events.
- Disconnected Tools: Most SOCs use dozens of different security tools (EDR, Firewalls, Email Security, IAM) that don’t communicate with each other. This requires analysts to swivel between consoles, manually collating data to build a complete picture of an incident.
- Manual, Repetitive Tasks: Activities like gathering host information, checking an IP’s reputation, isolating a machine from the network, or resetting a user’s credentials are often done manually. These steps are repeatable, predictable, and consume valuable time.
- Inconsistent Response: When response depends on manual actions, it varies based on the analyst’s experience and the time of day. This lack of standardization increases the risk of error.
The Duo: Defining SIEM and SOAR
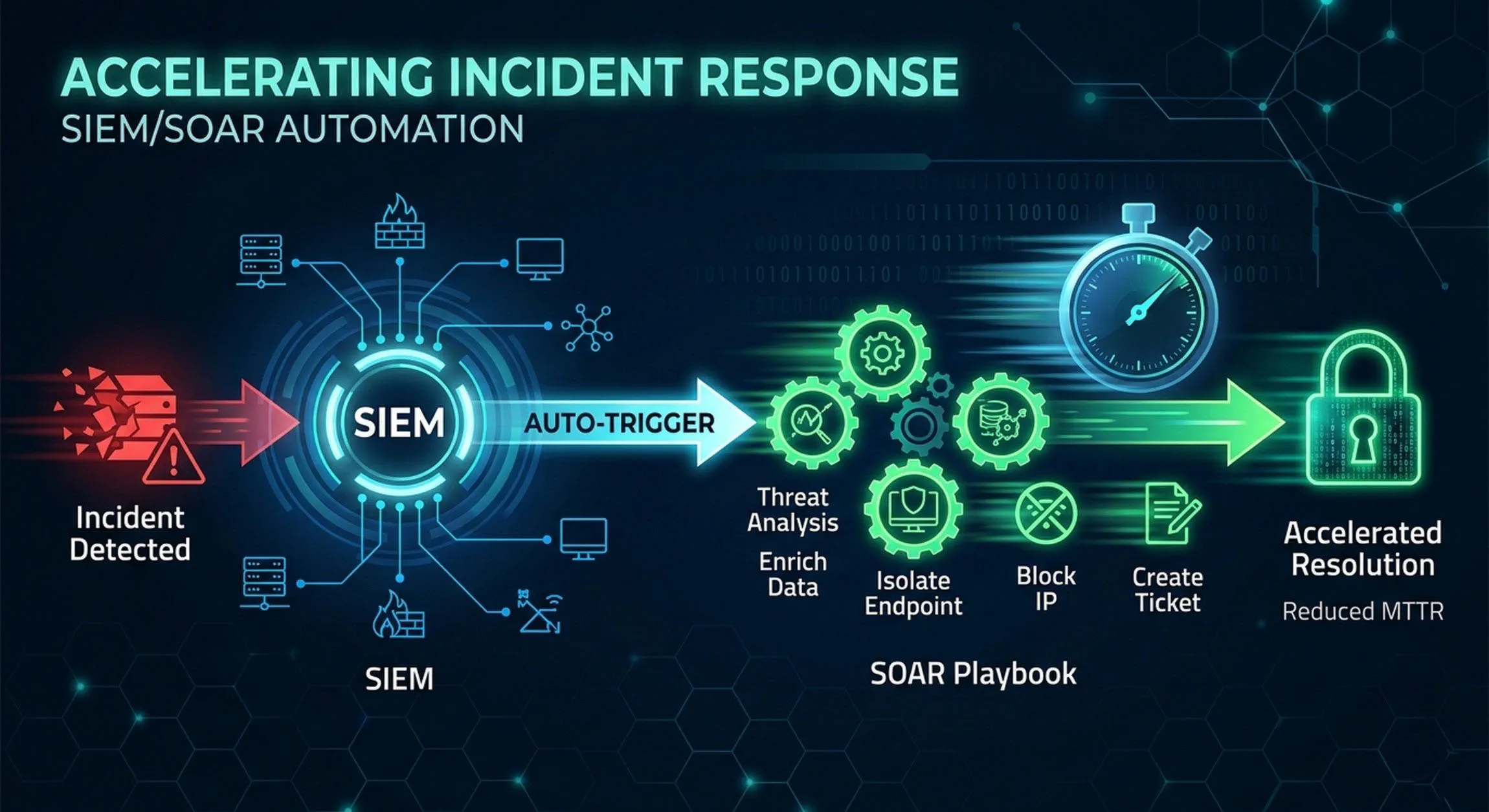
To accelerate your response, you need a system where detection seamlessly triggers action. This is achieved by combining two core technologies:
1. SIEM (Security Information and Event Management) - The Brain
A SIEM platform serves as the central “brain” of your SOC. It collects, normalizes, and correlates logs from across your entire infrastructure (network devices, servers, applications, cloud environments). Its primary function is to detect anomalies and potential threats by identifying patterns of malicious behavior that isolated tools might miss.
2. SOAR (Security Orchestration, Automation, and Response) - The Brawn
A SOAR platform provides the “brawn” and efficiency. It doesn’t just find threats; it acts on them. SOAR is the connective tissue that integrates your entire security stack, allowing tools from different vendors to work together. It uses predefined playbooks to automate repetitive, rule-based tasks and orchestrate complex response workflows.
| Feature | SIEM | SOAR |
|---|---|---|
| Primary Focus | Detection and Investigation | Response and Management |
| — | — | — |
| Data Action | Aggregates, Correlates, and Alerts | Orchestrates, Automates, and Triage |
| — | — | — |
| Primary Strength | Broad Network Visibility | Speed and Operational Consistency |
| — | — | — |
How SIEM and SOAR Work in Tandem
The integration of SIEM and SOAR creates a continuous loop of automated detection and response. Here is a typical workflow showing how they accelerate incident response:
- Detection: A SIEM rule detects a multi-stage attack pattern, such as a brute-force login attempt followed by rare process execution on a domain controller. The SIEM generates a high-fidelity alert.
- Trigger: Instead of waiting for a human analyst to see the alert, the SIEM automatically pushes the alert to the SOAR platform.
- Triage and Enrichment (Automated): The SOAR platform instantly triggers a predefined playbook. The playbook executes automated enrichment steps:
- Queries threat intelligence feeds to check the reputation of the source IP.
- Pulls user and asset data from Active Directory.
- Retrieves process details and user activity logs from the endpoint using EDR.
- Investigation (Semi-Automated): All this context is presented to the security analyst in a single, unified case file within seconds, eliminating the need for manual data gathering.
- Containment and Response (Orchestrated): If the incident matches defined parameters for a confirmed attack, the playbook can automatically execute containment actions:
- Blocks the malicious IP on the perimeter firewall.
- Isolates the compromised endpoint from the network via EDR.
- Suspends the compromised user account in IAM.
- Resolution: The analyst reviews the automated actions, performs any necessary final eradication steps, and closes the case, significantly reducing MTTR from hours or days to minutes.
Telemetry Engineering and Threat Hunting
Log collection is not a strategy. Pumping unstructured data into a SIEM drives up costs and induces alert fatigue. Architects must define exactly what telemetry is required to detect advanced persistent threats (APTs).
Leverage Kusto Query Language (KQL) to build precise detection logic. We do not need alerts for every failed login. We need alerts for anomalous geographic access followed by lateral movement attempts within the Kubernetes cluster.
- Baseline Normalcy: Use machine learning models within the SIEM to baseline normal network behavior.
- Correlate Identity and Network Data: Combine IAM logs with VPC flow logs. A compromised credential accessing restricted micro-segments demands immediate isolation.
Automating Containment via SOAR
Incident response requires speed. Manual triage guarantees data exfiltration. Integrate Security Orchestration, Automation, and Response (SOAR) platforms to execute containment playbooks at machine speed.
When the SIEM detects a compromised host, the SOAR platform must autonomously execute the following:
- Isolate the endpoint from the network using API calls to the EDR platform.
- Revoke active IAM sessions associated with the compromised user.
- Generate a snapshot of the virtual machine for forensic analysis.
- Open a high-priority ticket containing all correlated evidence for the SOC analyst.
This closed-loop system reduces the Mean Time to Respond (MTTR) from hours to seconds. As a CISA and CISSP, I measure architectural success by its resilience and auditability under attack. By integrating architecture design directly with SOC operations, we build resilient, self-healing networks capable of withstanding the modern threat landscape.
Key Use Cases for Automation
Starting your automation journey with high-frequency, well-understood scenarios provides the fastest return on investment.
1. Phishing Email Triage and Response
Phishing is the number one vector for breaches. Automated playbooks can ingest suspected phishing emails, parse them to extract indicators (URLs, file hashes, senders), check these indicators against threat intelligence, detonate attachments in a sandbox, and automatically delete the malicious email from all affected inboxes.
2. Endpoint Malware Containment
When an EDR tool detects a confirmed malware infection, a SOAR playbook can immediately take actions to stop lateral movement. It can isolate the infected host, query the SIEM to find other machines the host communicated with, and initiate a full scan on those machines-all without waiting for human intervention.
3. Suspicious Login Response
Anomalous logins, such as simultaneous logins from different countries, can be handled automatically. A SOAR playbook can enrich the alert, compare it against known user travel plans, and automatically enforce multi-factor authentication or temporarily disable the account, forcing the user to contact the help desk.
Best Practices for Accelerating Response
To get the most value from your SIEM/SOAR integration, follow these strategic guidelines:
- Focus on Process First, Not Technology: Automation cannot fix a broken process. Before writing a playbook, document your manual incident response procedures. Streamline them first, then automate the standardized steps.
- Start Small and Iterate: Do not try to automate your most complex SEV1 incident on day one. Start with a simple, common, low-risk process (e.g., suspicious IP blocking). Build success, then tackle more complex workflows.
- Define Playbooks and Runbooks: A playbook is the strategic approach to a type of incident. A runbook is the tactical, step-by-step technical instruction your SOAR tool can execute. Build modular runbooks (e.g., “Reset User Credentials”) that can be reused across different playbooks.
- Keep a Human in the Loop: Some actions are too sensitive to be fully automated. Identify “approval gates” where the automation pauses and requires a human analyst to click an “Approve” button before executing high-impact actions like disabling a critical server or blocking business-critical traffic.
Conclusion
Accelerating incident response is not a luxury; it’s a modern defense necessity. Attackers operate with code-level speed; a defense dependent purely on human intervention can no longer keep pace. By integrating SIEM’s unmatched visibility and detection capabilities with SOAR’s speed, orchestration, and automation, you empower your SOC to fight code with code. This transformation from reactive detection to proactive response reduces your MTTR, mitigates attack impact, and gives your analysts the time they need to focus on strategic defense.
About the Author Sam Jobes, CISA-CISSP, is a 20-year information security veteran specializing in enterprise security architecture, GRC automation, and building scalable infosec programs for high-growth technology companies.