Incident Response
- Show All Articles
- Active directory 1
- Ai 6
- Ai security 1
- Architecture 27
- Automation 3
- Bash 1
- C# development 1
- Ci cd 1
- Cloud security 4
- Compliance 1
- Continuous monitoring 1
- Critical infrastructure 1
- Data center 1
- Data governance 1
- Data pipelines 1
- Detection engineering 1
- Devsecops 4
- Docker 1
- Forensics 1
- Immutable infrastructure 1
- Incident response 6
- Infosec 29
- Infrastructure hardening 1
- Iso 27001 2
- Knowledge 2
- Kubernetes forensics 1
- Llm 2
- Mdr 1
- Micro segmentation 1
- Microsoft defender 1
- Mind maps 2
- Mitre attack 1
- Multi cloud 1
- Ngfw 1
- Nist 1
- On prem 1
- Operations 1
- Pac 2
- Policy as code 2
- Powershell 1
- Project 5
- Project management 2
- Prompting 1
- Proxmox 1
- Python 2
- Quantfinance 1
- Rag 2
- Red teaming 1
- Reg ex 1
- Risk management 3
- Sase 1
- Security 1
- Security operations 2
- Siem 4
- Soar 2
- Systems architecture 2
- Systemsarchitecture 2
- Vector database 1
- Zero trust 4
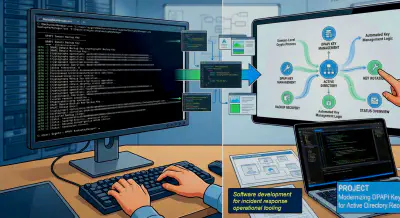
March 9, 2026
Operationalizing AD Recovery: A GUI Frontend for DPAPI Key Management
The Challenge: Cryptographic Persistence in Active Directory During an Active Directory compromise recovery, rotating …
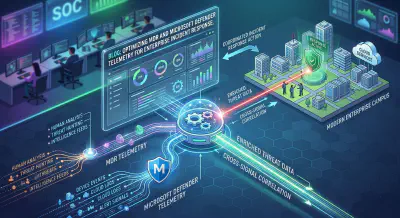
February 10, 2026
Optimizing MDR and Microsoft Defender Telemetry for Enterprise Incident Response
If there is one universal truth I have learned over two decades in information security, it is this: More data does not …
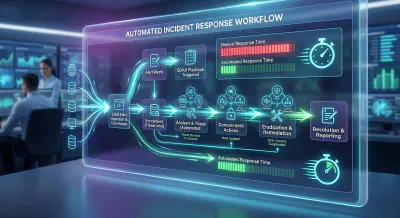
July 28, 2025
Architecting the Future of Defense: Your Guide to Automated Incident Response Pipelines
Architecting the Future of Defense In the high-stakes world of cybersecurity, time isn’t just money; it’s …

May 13, 2025
Engineering Audit-Ready Threat Detection: Integrating SIEM/SOAR with Risk Management
Engineering Audit-Ready Threat Detection Every Security Operations Center (SOC) manager knows the feeling. The auditor …
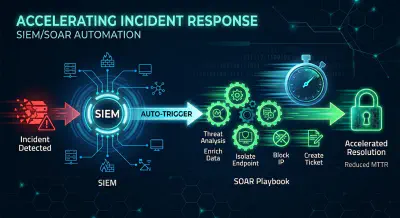
April 30, 2025
Stop the Clock: Accelerating Incident Response with SIEM and SOAR Automation
Accelerating Incident Response with SIEM and SOAR Automation In the digital age, a cybersecurity breach isn’t just …
April 7, 2025
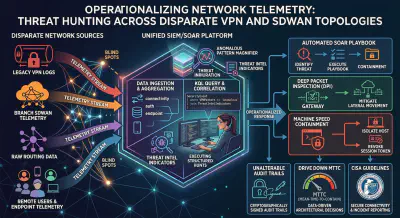
Operationalizing Network Telemetry: Threat Hunting Across Disparate VPN and SDWAN Topologies
Operationalizing Network Telemetry: Threat Hunting Across Disparate VPN and SDWAN Topologies Network visibility dictates …