Architecting SASE: Deprecating Legacy VPNs for Identity-Aware Micro-segmentation
The traditional network security model, centered around a hard perimeter defended by firewalls and virtual private network (VPN) concentrators, is fundamentally broken. In a “Cloud-First, Mobile-First” world, where users, devices, and applications are distributed globally, the concept of a single, trustworthy network perimeter is obsolete.
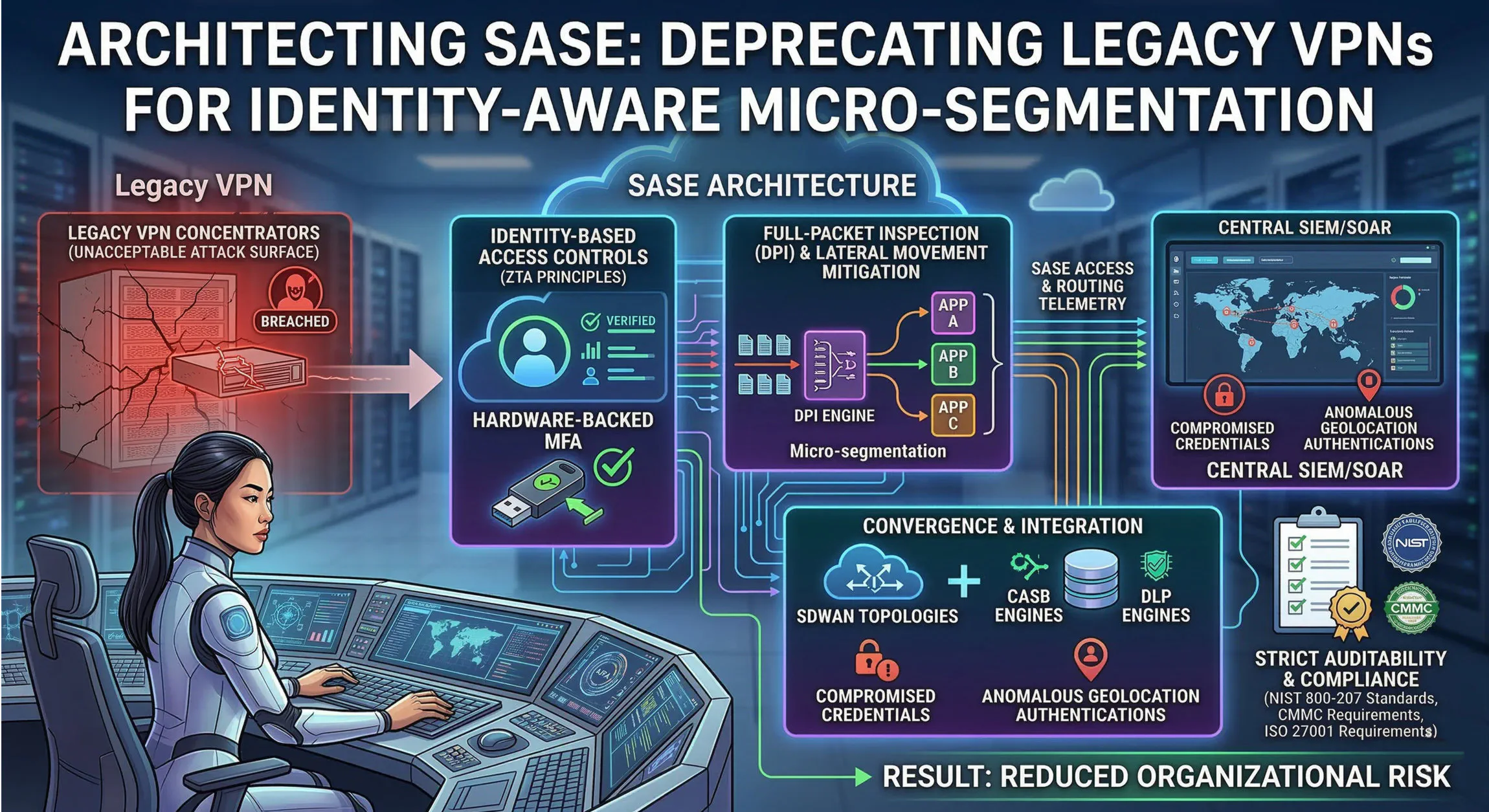
Continuing to rely on legacy VPN architecture introduces unacceptable risks. Once authenticated to a VPN concentrator, users are typically granted broad network-level access (Layer 3), allowing for unrestricted lateral movement across the internal environment. This “implicit trust” model is a primary vector for ransomware propagation and data exfiltration, as compromised credentials can grant attackers the keys to the kingdom.
Architects must embrace the inevitability of Security Service Edge (SSE) and Secure Access Service Edge (SASE) paradigms. The mandate is clear: deprecate perimeter-based defenses and transition remote access infrastructure to Zero-Trust Architecture (ZTA) principles.
The Case Against Legacy VPN Concentrators
Legacy VPN concentrators are a magnet for attackers. They present a large, often easily discoverable attack surface. Vulnerabilities in VPN software are frequently exploited for initial entry, and credential-stuffing attacks target the weak authentication common on many legacy deployments.
The core issue, however, isn’t just external vulnerability; it’s the internal architecture. Legacy VPNs create a binary trust boundary. You are either “outside” and untrusted, or “inside” and implicitly trusted. Once a user successfully authenticates via VPN, their device effectively becomes part of the corporate network, often with broad IP-level access to internal servers and databases.
This architecture directly contradicts the least-privilege principle. A user accessing a specific web application doesn’t need network-level visibility into domain controllers or internal development servers. In a legacy VPN model, they often get both.
Building a Zero-Trust Architecture with SASE and SSE
Architecting the transition requires a complete rethink of remote access. Zero-Trust Architecture (ZTA) must be the guiding principle, enforced through software-defined perimeters.
Identity-Aware Micro-segmentation
The fundamental shift is from network-based trust to identity-based access controls. Remote access must be granted at the application level (Layer 7), not the network level (Layer 3). When a user attempts to access a resource, the SASE fabric, utilizing SSE components, must verify the user’s identity, the device posture, and the specific application being requested.
This is achieved through identity-aware micro-segmentation. The traditional ‘perimeter’ is moved directly to the application itself. If a user is authorized for application A, they only connect to application A. Other applications on the same network subnet remain completely invisible to them. This deterministic access eliminates the possibility of lateral movement from a compromised endpoint, as the endpoint can only communicate with authorized destinations.
Security Service Edge (SSE): Unified Inspection Closer to the User
SSE components—Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), and Zero-Trust Network Access (ZTNA)—are critical in this architecture. They enforce security policies and inspect traffic close to the user and the data, in the cloud, before it ever reaches internal or SaaS resources.
Integrate full-packet inspection (DPI) not just at the edge, but within the SASE/SSE fabric. All traffic, including previously trusted east-west communication within data centers, must be subject to inspection to identify malicious payloads or unusual data movement. Security policies should enforce content inspection and malware scanning for all data entering or leaving the software-defined perimeter.
Hardware-Backed MFA: A Non-negotiable Prerequisite
The strength of your ZTA is only as strong as your identity provider. Relying on password-based authentication, even supplemented by SMS or mobile app push notifications, is insufficient for critical infrastructure. Modern attacks often utilize phishing to bypass standard multifactor authentication (MFA).
SASE deployment must mandate hardware-backed MFA (e.g., FIDO2 security keys) as an absolute requirement prior to session establishment. This authentication must occur before any policy check or posture assessment, ensuring that compromised credentials alone cannot grant access, even with a compliant device.
Converging Network and Security: SD-WAN and SSE Integration
SASE is the convergence of networking and security. Achieving unified policy enforcement requires integrating SD-WAN topologies directly with SSE security engines.
Branch offices and remote users should route traffic via SD-WAN to the closest SSE point of presence (PoP). There, all internet, SaaS, and internal traffic is subject to unified policy inspection. Connect SD-WAN routers directly with Cloud Access Security Brokers (CASB) to enforce fine-grained controls over SaaS application usage and data sharing. Furthermore, integrate Data Loss Prevention (DLP) engines to prevent sensitive data from leaving authorized perimeters, regardless of whether the endpoint is physically in an office or a coffee shop.
This convergence ensures that policy enforcement remains consistent and centralized, regardless of the endpoint’s physical location. Security is delivered as a cloud service, abstracting the complexities of underlying network infrastructure.
Gaining Telemetry and Detecting Anomalies
Centralized visibility is the lifeblood of a ZTA. Route all routing and access telemetry from the SASE fabric, SD-WAN devices, SSE endpoints, and identity providers to a central SIEM/SOAR platform. This creates a unified dataset for analysis and response.
Once aggregated, query anomaly detection datasets using powerful query languages like KQL. Develop detections to identify:
- Compromised Credentials: Anomalous login patterns, impossible travel scenarios, or password-spraying attempts across multiple applications.
- Anomalous Geolocation Authentications: Access attempts from unexpected countries or regions, especially those with high threat actor activity.
- Atypical User Behavior: Sudden spikes in data access, access to unusual resources, or attempts to access blocked applications.
Automate incident response using SOAR playbooks to automatically revoke access, isolate devices, or enforce re-authentication upon the detection of high-confidence anomalies.
Ensuring Compliance and Deterministic Risk Reduction
Architects must ensure all SASE deployment configurations map directly to established security standards. Utilize the NIST 800-207 “Zero Trust Architecture” guidelines as a blueprint for implementation, ensuring that implicit trust is systematically removed from every component.
Maintain strict auditability across the entire SASE and ZTA ecosystem. The centralized SIEM/SOAR platform must be configured to provide immutable audit trails of all access requests, policy decisions, authentication events, and security detections. This granular level of logging is essential to support ongoing compliance with complex requirements such as CMMC (Cybersecurity Maturity Model Certification) and ISO 27001.
By architecting SASE and ZTA to enforce deterministic, software-defined perimeters based on identity, organizations can drastically reduce their attack surface and mitigate the risk of catastrophic breaches. The era of static network defenses is over; the future is software-defined and identity-aware.