Architecture
- Show All Articles
- Active directory 1
- Ai 6
- Ai security 1
- Architecture 27
- Automation 3
- Bash 1
- C# development 1
- Ci cd 1
- Cloud security 4
- Compliance 1
- Continuous monitoring 1
- Critical infrastructure 1
- Data center 1
- Data governance 1
- Data pipelines 1
- Detection engineering 1
- Devsecops 4
- Docker 1
- Forensics 1
- Immutable infrastructure 1
- Incident response 6
- Infosec 29
- Infrastructure hardening 1
- Iso 27001 2
- Knowledge 2
- Kubernetes forensics 1
- Llm 2
- Mdr 1
- Micro segmentation 1
- Microsoft defender 1
- Mind maps 2
- Mitre attack 1
- Multi cloud 1
- Ngfw 1
- Nist 1
- On prem 1
- Operations 1
- Pac 2
- Policy as code 2
- Powershell 1
- Project 5
- Project management 2
- Prompting 1
- Proxmox 1
- Python 2
- Quantfinance 1
- Rag 2
- Red teaming 1
- Reg ex 1
- Risk management 3
- Sase 1
- Security 1
- Security operations 2
- Siem 4
- Soar 2
- Systems architecture 2
- Systemsarchitecture 2
- Vector database 1
- Zero trust 4

April 26, 2026
A Thousand and One Nights - 1,000 Security Prompts to Improve Your Workflow
A Thousand and One Nights Looking for ideas on how to use AI to assist with your security workload?
The following is a …
March 12, 2026
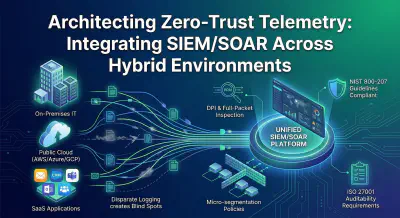
Architecting Zero-Trust Telemetry: Integrating SIEM/SOAR Across Hybrid Environments
Architecting Zero-Trust Telemetry: Integrating SIEM/SOAR Across Hybrid Environments In today’s hyper-connected, …
March 11, 2026
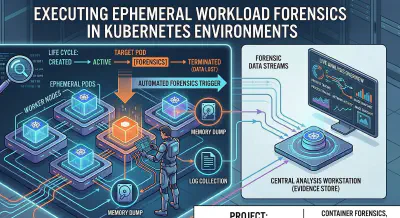
Executing Ephemeral Workload Forensics in Kubernetes Environments
When I started in information security over two decades ago, digital forensics was a highly tactile discipline. We …
March 9, 2026
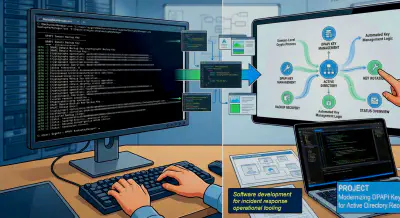
Operationalizing AD Recovery: A GUI Frontend for DPAPI Key Management
The Challenge: Cryptographic Persistence in Active Directory During an Active Directory compromise recovery, rotating …
March 5, 2026
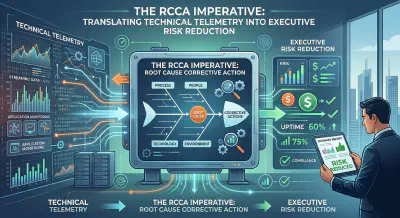
The RCCA Imperative: Translating Technical Telemetry into Executive Risk Reduction
In my two decades navigating the ever-shifting landscape of information security, I have witnessed countless evolutions …

March 3, 2026
Advanced Host and Network Forensics: Weaponizing EDR and DPI Telemetry
Executive Summary In the modern threat landscape, sophisticated adversaries thrive in the gaps between traditional …

February 20, 2026
Scaling Global CIRT Capabilities: Standardizing Cross-Platform Triage
Scaling Global CIRT Capabilities: Standardizing Cross-Platform Triage Twenty years in the information security trenches …
February 10, 2026
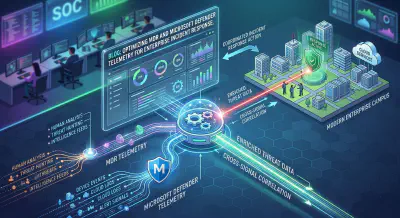
Optimizing MDR and Microsoft Defender Telemetry for Enterprise Incident Response
If there is one universal truth I have learned over two decades in information security, it is this: More data does not …
January 17, 2026
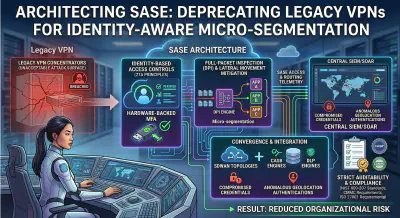
Architecting SASE: Deprecating Legacy VPNs for Identity-Aware Micro-segmentation
Architecting SASE: Deprecating Legacy VPNs for Identity-Aware Micro-segmentation The traditional network security model, …

January 14, 2026
From Buzzword to Blueprint: Operationalizing Zero-Trust Across On-Premise and Multi-Cloud Environments
From Buzzword to Blueprint: Operationalizing Zero-Trust Across On-Premise and Multi-Cloud Environments For years, …
December 22, 2025
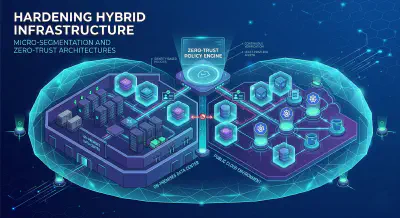
Hardening Hybrid Infrastructure: Micro-Segmentation and Zero-Trust Architectures
Hardening Hybrid Infrastructure As organizations race to embrace the flexibility and scalability of hybrid cloud …
December 5, 2025
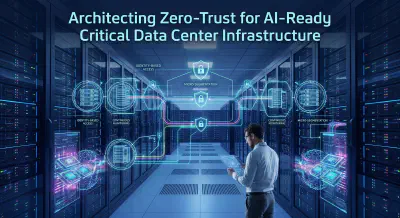
Architecting Zero-Trust for AI-Ready Critical Data Center Infrastructure
If you’ve spent any time in the trenches of enterprise architecture over the last two years, you already know the truth: …
December 2, 2025
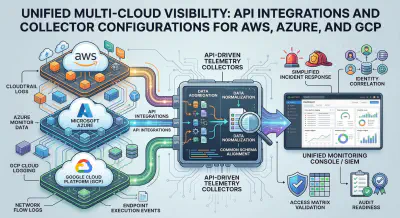
Unified Multi-Cloud Visibility: API Integrations and Collector Configurations for AWS, Azure, and GCP
Unified Multi-Cloud Visibility: API Integrations and Collector Configurations for AWS, Azure, and GCP Modern enterprise …

November 22, 2025
Operationalizing Continuous Compliance for ISO 27001, SOC 2, and PCI
Executive Summary: Operationalizing Continuous Compliance for ISO 27001, SOC 2, and PCI A strategic shift from …

November 11, 2025
Taming the Exception Beast: Structuring Defensible Risk Exception Workflows Under NIST and ISO 27001
Executive Summary In the realm of information security governance, the road to audit failure is often paved with good …
October 24, 2025
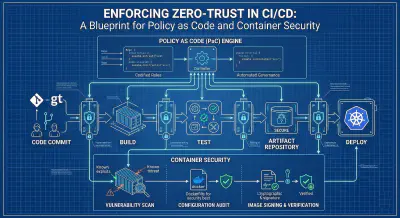
Enforcing Zero-Trust in CI/CD: A Blueprint for Policy as Code and Container Security
Enforcing Zero-Trust in CI/CD The DevOps revolution promises unprecedented speed and agility, allowing organizations to …
October 16, 2025
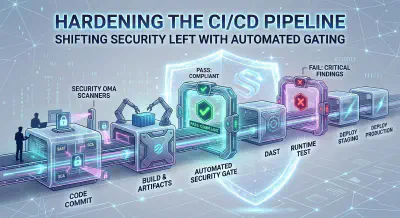
Hardening the CI/CD Pipeline: Shifting Security Left with Automated Gating
Hardening the CI/CD Pipeline In the modern era of software development, velocity is king. Organizations are racing to …

October 15, 2025
Metrics-Driven Security: Building Automated Reporting and Telemetry Health Checks
Metrics-Driven Security: Building Automated Reporting and Telemetry Health Checks In today’s complex cyber threat …
September 5, 2025
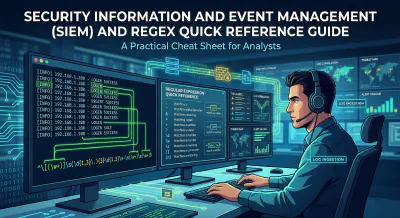
Security Information and Event Management (SIEM) and Regex Quick Reference Guide
Executive Summary The following is a technical overview of SIEM architecture, data ingestion methods, and simple Regular …
August 30, 2025
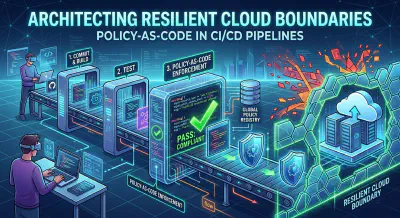
Architecting Resilient Cloud Boundaries: Policy-as-Code in CI/CD Pipelines
Architecting Resilient Cloud Boundaries The traditional concept of a rigid network perimeter-the “castle and …
July 25, 2025
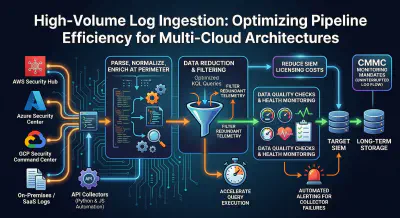
High-Volume Log Ingestion: Optimizing Pipeline Efficiency for Multi-Cloud Architectures
High-Volume Log Ingestion: Optimizing Pipeline Efficiency for Multi-Cloud Architectures In the modern landscape of …
June 18, 2025
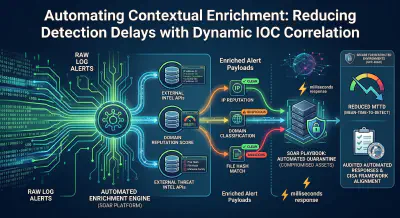
Automating Contextual Enrichment: Reducing Detection Delays with Dynamic IOC Correlation
Automating Contextual Enrichment: Reducing Detection Delays with Dynamic IOC Correlation By [Your Name/Title]
False …
June 13, 2025
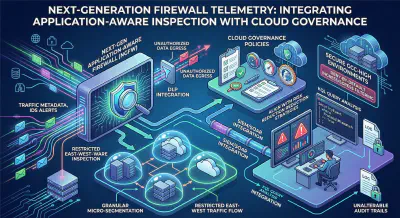
Next-Generation Firewall Telemetry: Integrating Application-Aware Inspection with Cloud Governance
Next-Generation Firewall Telemetry: Integrating Application-Aware Inspection with Cloud Governance Port-based firewall …

May 13, 2025
Engineering Audit-Ready Threat Detection: Integrating SIEM/SOAR with Risk Management
Engineering Audit-Ready Threat Detection Every Security Operations Center (SOC) manager knows the feeling. The auditor …
April 7, 2025
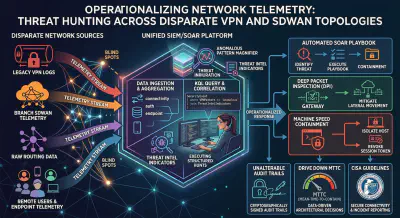
Operationalizing Network Telemetry: Threat Hunting Across Disparate VPN and SDWAN Topologies
Operationalizing Network Telemetry: Threat Hunting Across Disparate VPN and SDWAN Topologies Network visibility dictates …
January 21, 2025
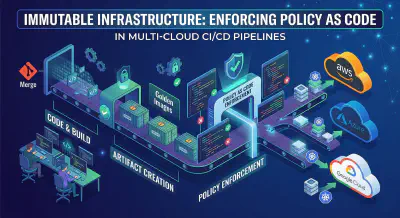
Immutable Infrastructure: Enforcing Policy as Code in Multi-Cloud CI/CD Pipelines
The Paradigm Shift to Policy as Code Manual security reviews bottleneck engineering velocity. Architects must embed …

January 8, 2025
Taming the Multi-Cloud Beast: Architecting Security by Aligning ZTA, NIST, and ISO 27001
Taming the Multi-Cloud Beast The mandate for modern enterprise IT is clear: agility requires a multi-cloud strategy. …