Architecting Zero-Trust Telemetry: Integrating SIEM/SOAR Across Hybrid Environments
In today’s hyper-connected, hybrid enterprise landscape, the traditional perimeter-based security model is not just insufficient—it’s obsolete. The rise of cloud services, remote work, and distributed applications has rendered the classic ‘castle-and-moat’ approach ineffective against sophisticated, modern threats. The prevailing security paradigm must shift towards Zero-Trust Architecture (ZTA). A critical, yet often underappreciated, pillar of successful ZTA implementation is comprehensive and unified telemetry. You cannot defend what you cannot see, and you cannot verify when your visibility is fragmented. Visibility defines defense.
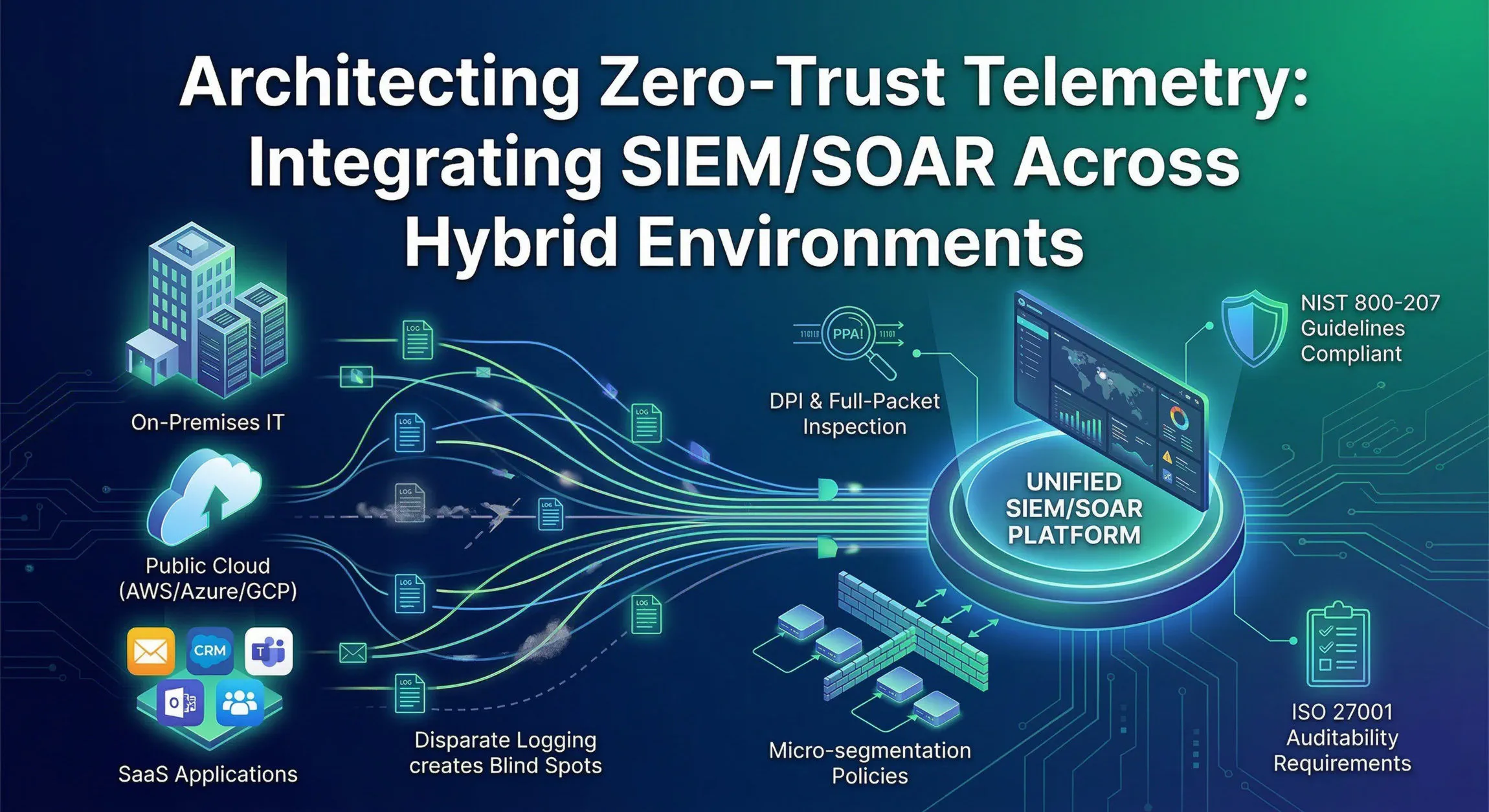
Modern enterprises require unified telemetry across hybrid environments to truly enforce ZTA principles. The premise is simple: never trust, always verify, based on all available data. Achieving this level of continuous, contextual verification necessitates consolidating disparate logging streams—from endpoints and perimeter gateways to various SaaS applications—into a centralized Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platform.
The Challenge of Hybrid Visibility and the Cost of Blind Spots
Hybrid environments, by their nature, are diverse and complex. They combine legacy on-premises infrastructure, private clouds, multiple public cloud providers (AWS, Azure, GCP), and a multitude of SaaS applications (Office 365, Salesforce, Slack, etc.). Each of these environments generates vast amounts of security telemetry, but often in siloed systems, using different formats, and offering varying levels of granularity.
Disparate logging creates blind spots—critical gaps in your visibility where attackers can operate undetected. These blind spots significantly increase your mean time to detect (MTTD) and mean time to respond (MTTR), allowing threats to dwell longer within your network and maximizing potential damage.
Without unified telemetry, correlate events across a user’s initial access (perhaps via a phishing email into a SaaS app), lateral movement to an on-prem server, and subsequent data exfiltration to a public cloud storage bucket becomes a monumental challenge, if not impossible. Security teams spend valuable time manually stitching together alerts, leading to alert fatigue and missed context.
Consolidating Logs into SIEM/SOAR: The Visibility Backbone
The first step in architecting Zero-Trust telemetry is centralizing all security-relevant logs into a unified platform. Modern cloud-native SIEMs are ideally suited for this task, offering the scalability and analytical power needed to handle the volume and velocity of hybrid data.
Comprehensive Log Ingestion Strategy
To eliminate blind spots, your log ingestion strategy must be comprehensive. Key data sources include:
- Endpoints: Ingest detailed logs from EDR (Endpoint Detection and Response) agents, host firewalls, and operating system event logs (Sysmon on Windows is crucial for rich process-level visibility). Focus on process execution, network connections, file integrity, and user activity.
- Perimeter Gateways: Collect logs from firewalls, VPN gateways, and Secure Web Gateways (SWGs). Look beyond simple ‘allow/deny’ logs; focus on session duration, bytes transferred, and deep-packet insights where available.
- SaaS Applications: Leverage API-based connectors to ingest audit logs from SaaS providers. Monitor user logins (including MFA events), data access, permission changes, and configuration modifications.
- Cloud Infrastructure: Utilize native cloud logging services (e.g., AWS CloudTrail/VPC Flow Logs, Azure Monitor/Network Security Group flow logs) to capture control plane and data plane activity within your public cloud environments. Focus on IAM changes, resource creation/deletion, and network traffic flow.
- Identity Providers (IdPs): Central to Zero Trust, ingest authentication logs from IdPs like Okta, Azure AD, or Ping Identity. Track successful and failed logins, authentication methods used, and potential compromise indicators.
Standardizing Log Ingestion Protocols
Standardization is vital for efficient normalization and correlation. Prioritize standard protocols wherever possible:
- Syslog: The workhorse for network devices and Unix/Linux systems. Ensure you are using secure, reliable transport like Syslog-over-TLS.
- CEF (Common Event Format) / LEEF (Log Event Extended Format): Standard formats supported by many vendors that facilitate parsing.
- API Pollers/Webhooks: Increasingly common, especially for SaaS applications and cloud native services, offering near real-time ingestion.
By normalizing these diverse logs into a common schema (e.g., Elastic Common Schema or Splunk’s Common Information Model), you transform raw data into a powerful asset, enabling efficient querying and robust cross-device correlation.
Enhancing Detection and Response with SIEM and SOAR
Centralization alone is insufficient; you must unlock the value within that data.
Deep Packet Inspection (DPI) at Perimeter Gateways
To mitigate lateral movement, simple port-and-protocol firewalls are inadequate. Implement full-packet inspection (DPI) at your perimeter and internal segment gateways. DPI enables you to:
- Inspect Application-Layer Payloads: Look inside the data stream to identify malicious traffic disguised as legitimate application protocols (e.g., command-and-control communication over DNS or HTTPs).
- Identify Protocol Anomalies: Detect non-standard or malicious uses of protocols, which are common indicators of compromise or reconnaissance.
- Stop Malicious Payloads: Leverage DPI capabilities for real-time intrusion prevention (IPS) to block known exploits and malware delivery.
Integrating DPI telemetry into your SIEM provides crucial context on how an asset is communicating, far exceeding simple ‘source IP to destination IP’ flow logs.
Implementing Automation with SOAR
SOAR platforms take this centralized visibility and convert it into action. Automated playbooks can ingest alerts from the SIEM and execute predefined responses, dramatically speeding up containment and remediation.
Example SOAR Use Cases for Zero Trust:
- Automated Containment: Upon detecting a high-fidelity endpoint alert (e.g., credential dumping), a SOAR playbook can automatically isolate the host from the network.
- Account Lockdown: Following multiple failed login attempts from a risky location (detected by IdP telemetry in SIEM), SOAR can temporarily disable the user account and trigger a ticket for investigation.
- Policy Update: If the SIEM correlates traffic to a known malicious IP from multiple internal segments, SOAR can automatically push a new firewall rule to block that IP across all relevant gateways.
Aligning Telemetry with Standards and Policies
Zero Trust isn’t just a technical configuration; it’s a strategic framework that should be guided by industry standards and compliance requirements.
Mapping Detection Logic to NIST 800-207
The NIST SP 800-207 “Zero Trust Architecture” guidelines are foundational. Ensure that your detection logic and security policies directly support these principles. Map your SIEM detection rules to address:
- Resource Access Requests: Use telemetry to verify the subject (user/device identity, security posture) and the resource (SaaS app, internal database) against policy before granting access.
- Continuous Monitoring: Verify the security posture of an established connection continuously, not just at login. Leverage EDR and network telemetry to detect drift.
- Micro-Segmentation: Implement and enforce granular segmentation policies based on real-time asset behavior telemetry, limiting lateral movement. For example, a development server should only communicate with its database and necessary build systems, never directly with accounting workstations. Use flow logs and asset inventories within the SIEM to identify and validate these segments.
Maintain Auditability for ISO 27001 Requirements
Stringent access control and comprehensive logging are critical to satisfying ISO/IEC 27001 auditability requirements. Unified telemetry is indispensable here:
- User and Admin Activity Monitoring: Use SIEM reports to demonstrate that you are monitoring all critical user activities and administrative actions, directly supporting Annex A controls.
- Access Control Verification: Periodically review logs in the SIEM to verify that access control policies are being enforced correctly and that only authorized users/devices are accessing sensitive resources.
- Incident Investigation: In the event of an incident, the centralized log repository becomes the primary evidence source for root cause analysis and impact assessment, crucial for meeting both internal investigation needs and regulatory reporting obligations.
Conclusion
Achieving unified visibility in a complex hybrid environment is non-negotiable for a functioning Zero-Trust Architecture. By architecting a robust telemetry pipeline, centralizing diverse logs into a sophisticated SIEM/SOAR platform, and enforcing granular, behavior-based policies, organizations can effectively eliminate blind spots and move towards a proactive, resilient security posture.
Do not allow visibility gaps to compromise your organization’s security and compliance posture. Take the decisive first step towards true Zero-Trust observability today. Evaluate your existing logging strategies and prioritize consolidating visibility across your endpoints, networks, and cloud applications. Contact our solution experts to learn how our advanced SIEM and SOAR solutions can help accelerate your journey to unified hybrid security.