Architecting Resilient Cloud Boundaries
The traditional concept of a rigid network perimeter-the “castle and moat” model-is effectively dead in the era of dynamic, multi-cloud infrastructure. Your cloud environment is not a single location; it’s a fluid ecosystem of interconnected services, APIs, serverless functions, and distributed applications spread across vast virtual boundaries.
In this reality, relying on manual processes or static, network-based controls (like basic security groups or VPC peering) to define and maintain your boundaries is a recipe for catastrophic failure. These boundaries are necessary, but they are too slow and error-prone on their own. Human misconfiguration remains the single largest source of cloud data breaches.
True resilience in the cloud doesn’t just mean a system can withstand an attack. It means engineering the system so it cannot be misconfigured into an vulnerable state. This is where architecting resilient cloud boundaries requires Policy-as-Code (PaC), and embedding it directly into the heart of your engineering lifecycle: the CI/CD pipeline.
The Friction of Static Boundaries in a Dynamic World
Static cloud boundaries fail because they rely on human governance in an environment moving at machine speed. A developer needing to deploy a new microservice might spin up a Kubernetes cluster with default settings that expose management APIs, or create an S3 bucket and unintentionally make it public while testing.
By the time a central security team (if you have one) manually audits this configuration weeks later, the damage could already be done. Relying on out-of-band monitoring and remediation is reactive and insufficient for resilience. You need proactive enforcement.
Enter Policy-as-Code (PaC)
Policy-as-Code is the practice of managing and enforcing policies-security, compliance, and operational best practices-using machine-readable files (code) rather than manual checklists.
Think of it as the legal code of your infrastructure, written in languages like Rego (used by Open Policy Agent, OPA), Sentinel, or even native validations within Terraform. PaC allows you to define policies declaratively, version-control them in Git, and test them just like application code.
A simple conceptual policy example:
\# Hypothetical OPA Rego policy to block public S3 buckets
package cloud_boundaries
deny\[msg\] {
\# Match resources of type aws_s3_bucket
input.resource_type == "aws_s3_bucket"
\# Identify buckets where public access is enabled
input.attributes.acl == "public-read"
msg = sprintf("S3 bucket '%v' is configured for public read access. This is denied.", \[input.attributes.name\])
}
This code doesn’t just document a rule; it becomes an automated check that can make decisions in real-time.
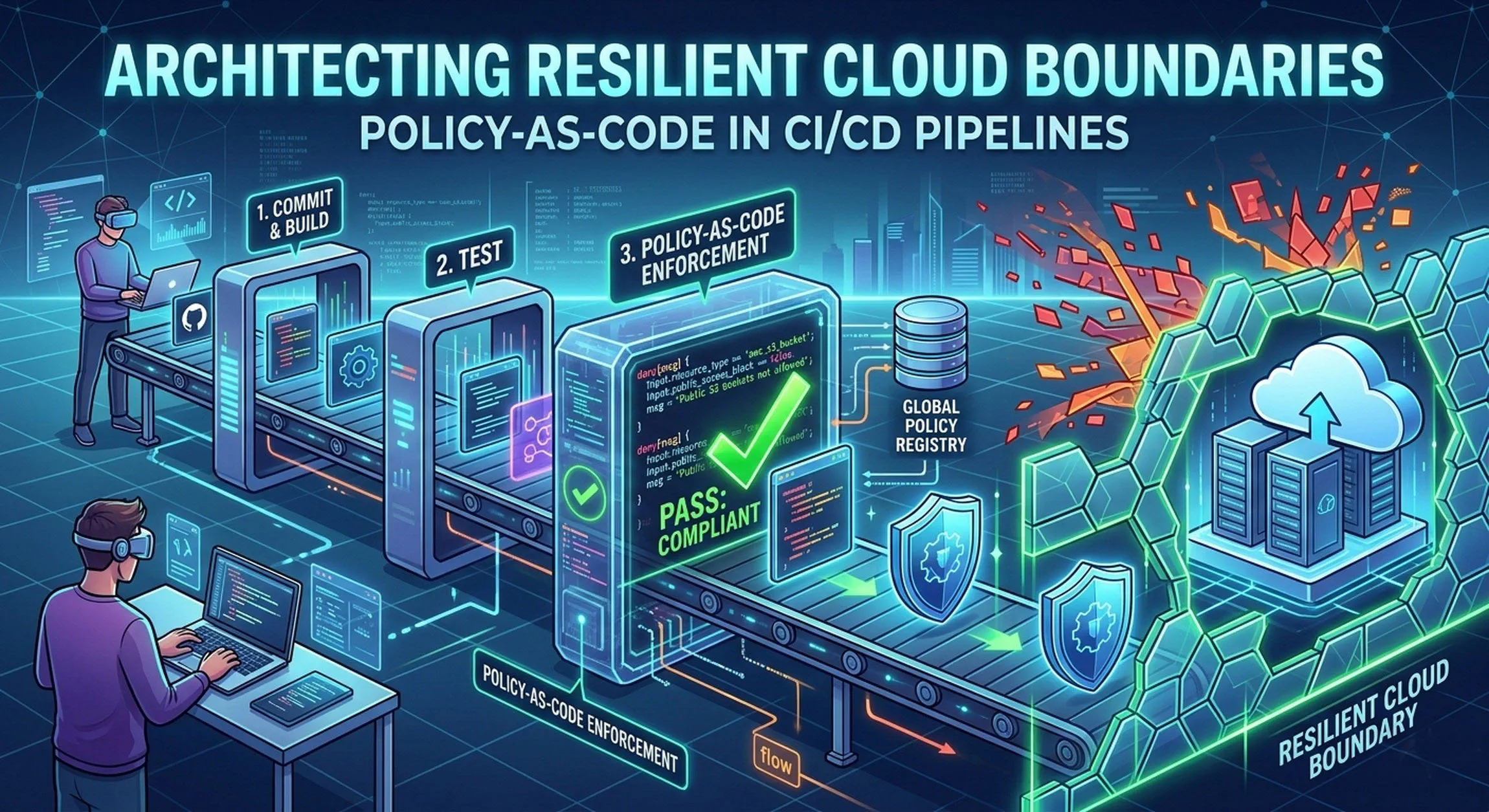
The Resilient CI/CD Flow: Shift Left and Continuous Enforcement
The power of Policy-as-Code is unlocked when you integrate it into your Continuous Integration and Continuous Deployment (CI/CD) pipelines. This concept is often called DevSecOps, but specifically, it facilitates Compliance-as-Code or Infrastructure-as-Code (IaC) Validation.
Integrating PaC creates a resilient boundary by shifting security and compliance enforcement to the left-as early in the development lifecycle as possible.
The Automated Workflow for Resilience
- Code Commit: A developer defines new infrastructure changes (e.g., using Terraform to create a new VPC boundary and security groups) and commits the IaC to Git.
- The CI Phase (The Guardrail): The commit triggers the CI pipeline. The pipeline pulls the definition of the planned infrastructure and runs it through a Policy Engine (like OPA).
- Example 1: The engine checks IAM roles defined in the IaC against a “least privilege” policy (e.g., “Deny IAM roles with administrative access if not tagged as ’emergency’”).
- Example 2: It validates the new security group rules (e.g., “Deny security group rules allowing inbound SSH (port 22) from 0.0.0.0/0”).
- Example 3: It validates network segmentation boundary rules (e.g., “A database subnet boundary must not allow direct inbound traffic from an external internet gateway”).
- Feedback & Blocking:
- If the IaC definition violates a policy, the pipeline fails. The developer receives immediate feedback (e.g., “Build failed: IAM role ‘dev-role’ violates Least Privilege Policy #11”). The misconfiguration never proceeds to deployment.
- If the IaC passes all policy checks, the pipeline continues.
- The CD Phase (Enforcement): Only validated, compliant code is allowed to be deployed to the cloud environment. The deployment process is automated, ensuring the boundary defined in the tested code is exactly what is instantiated in production.
Architecting the Resilient Boundary Stack
To build this resilient boundary architecture, you need three key components:
- Infrastructure-as-Code (IaC): Tools like Terraform, AWS CloudFormation, or Azure ARM templates provide the machine-readable definition of your cloud boundaries.
- Policy Engine: The engine that executes the code. Open Policy Agent (OPA) is a CNCF graduated project and a popular, vendor-agnostic choice. Sentinel (by HashiCorp) is integrated tightly into Terraform Enterprise.
- CI/CD Platform: Automation systems like GitHub Actions, GitLab CI, or Jenkins orchestrate the flow, running the policy checks between the IaC plan and application phases.
Conclusion: Engineering Impossibility
Architecting resilient cloud boundaries is no longer a question of if you use Policy-as-Code, but how deeply you integrate it. By treating security and compliance policies as automated guardrails within your CI/CD pipeline, you stop trying to fix misconfigurations and start preventing them entirely.
You move from a world where resilience is maintained by heroic effort to a world where resilience is maintained by design. You create a system where engineering an vulnerable boundary is not just discouraged-it is impossible.