Automating Contextual Enrichment: Reducing Detection Delays with Dynamic IOC Correlation
By [Your Name/Title]
False positives degrade analyst performance. This is a cold, hard fact in modern security operations. Security Operations Centers (SOCs) are drowning in alerts, many of which are benign, redundant, or lack sufficient context to be actionable. The traditional approach—manual alert triage and validation—is not just inefficient; it’s a critical vulnerability. Every minute an analyst spends manually investigating a false positive is a minute they are not hunting for real threats or responding to actual incidents.
The solution isn’t to hire more analysts or tune out more alerts (though tuning is necessary). The solution is to change how alerts are presented and validated. Security teams must stop manually validating alerts and embrace automation to provide the crucial context needed to separate signal from noise.
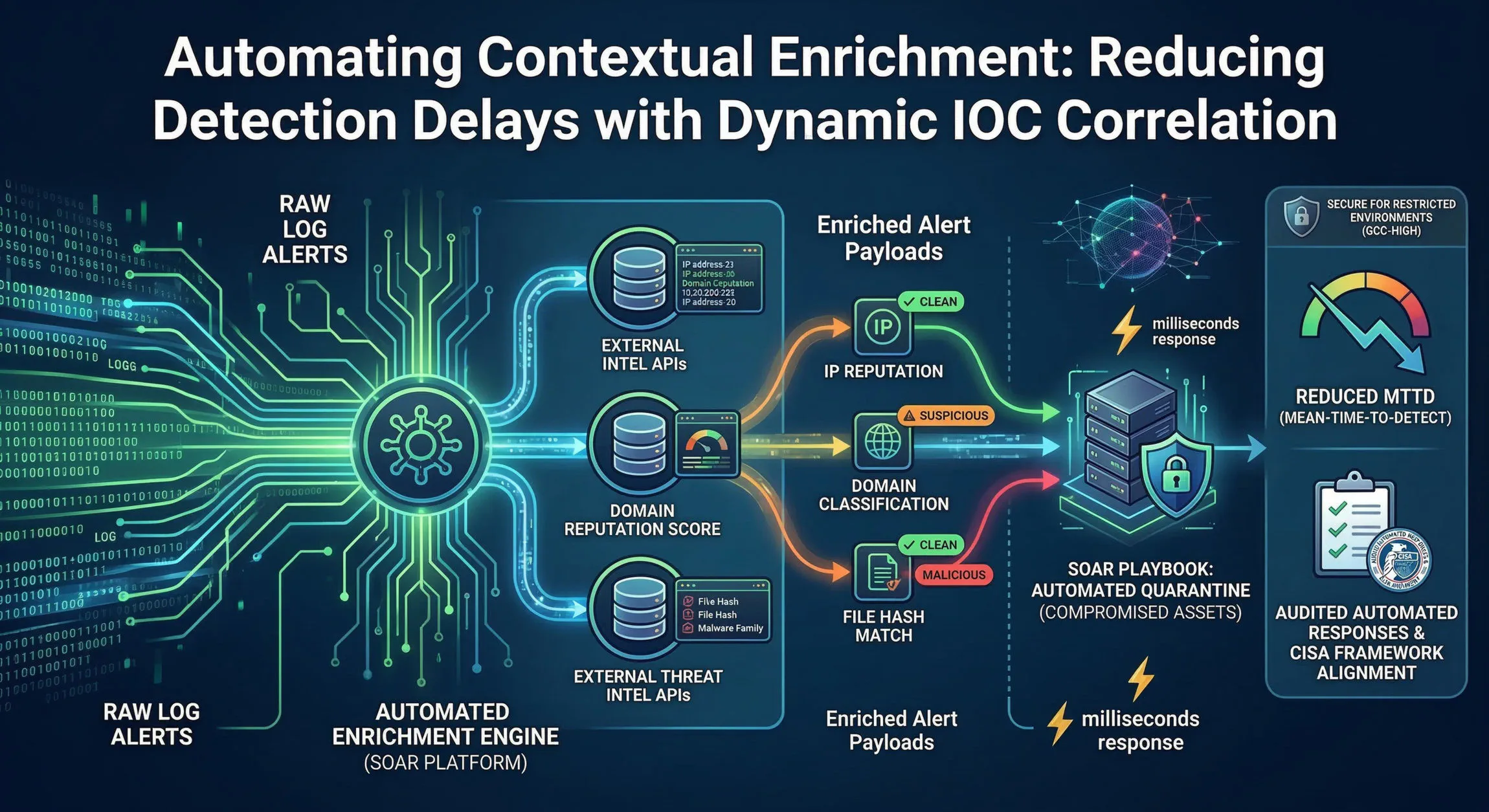
This article explores how to architect an automated contextual enrichment pipeline using dynamic Indicators of Compromise (IOC) correlation. By appending real-time, external threat intelligence directly to alert payloads and triggering automated responses via Security Orchestration, Automation, and Response (SOAR) playbooks, organizations can dramatically reduce detection delays and improve their overall security posture.
The Core Problem: Alert Fatigue and Delayed Detection
Traditional security monitoring often follows a predictable, flawed pattern:
- A security tool (EDR, SIEM, Firewall) generates an alert based on a specific event (e.g., a process execution, a network connection).
- The alert is sent to a central console (SIEM or SOAR).
- The alert payload often contains minimal context: timestamp, source/destination IP, hostname, perhaps a file hash or process name.
- An analyst receives the alert and must then manually gather additional information to determine its validity:
- What is the reputation of this IP?
- Is this a known malicious domain?
- Does this file hash correspond to a known malware family?
- What are the specific capabilities of this potential malware?
- Is this activity expected behavior for this user or asset?
This manual investigation introduces significant delays. The time between initial detection and definitive validation can stretch from minutes to hours. This delay, known as the Mean Time To Detect (MTTD), is a critical metric. The longer a threat actor operates undetected, the more damage they can inflict.
Furthermore, this manual process contributes heavily to alert fatigue. Analysts, overwhelmed by a constant barrage of alerts—many of which turn out to be false positives after tedious investigation—may become desensitized. This desensitization can lead to genuine, critical alerts being overlooked or delayed, with potentially catastrophic consequences.
Automating Contextual Enrichment: The Solution
Automated contextual enrichment addresses these issues head-on. The goal is to append actionable, high-fidelity information to an alert before it is ever presented to an analyst. When the analyst finally views the alert, they are presented not just with the raw event data, but with a enriched payload that answers many of their initial investigative questions.
This is achieved by integrating the SIEM or SOAR platform with external threat intelligence APIs and internally configured logic.
Architectural Blueprint for Enrichment
A robust enrichment architecture typically involves a multi-stage pipeline:
- Alert Ingestion and Parsing: The SIEM or SOAR platform ingests an alert from a security tool. The payload is parsed to extract key artifacts (IOCs) such as:
- IPv4/IPv6 Addresses
- Fully Qualified Domain Names (FQDNs) / URLs
- File Hashes (MD5, SHA-1, SHA-256)
- Email Addresses
- Usernames
- Hostnames/Asset IDs
- Enrichment Triggering (Logic/Playbook): A pre-configured logic rule or SOAR playbook is triggered based on specific alert criteria (e.g., a certain alert type, severity, or source tool).
- Threat Intelligence Lookup: For each extracted IOC, the enrichment engine initiates simultaneous API requests to configured threat intelligence providers. Examples include:
- Public Repositories: VirusTotal (for file hash and URL reputation), AbuseIPDB (for IP reputation), Cisco Umbrella (for domain classification).
- Commercial Feeds: CrowdStrike Falcon Intelligence, Recorded Future, ThreatConnect (for in-depth adversary context and attribution).
- Internal Data: Correlating against internal asset databases, configuration management databases (CMDBs), and past incident history.
- Data Processing and Contextualization: The responses from the threat intelligence APIs are parsed and processed. The system extracts relevant information, such as:
- Reputation Score: A numerical or categorized score indicating the likelihood of malice (e.g., “Malicious,” “Suspicious,” “Harmless”).
- Association: Malware family names, threat actor attribution, known campaigns.
- Capabilities/TTPs: Documented behaviors associated with the IOC (e.g., “Persistence via registry run keys,” “C2 communication over port 80/443”).
- First/Last Seen: Historical context for the IOC.
- Payload Appending and Correlation: The processed, contextual information is directly appended to the alert payload or correlated as related entities within the SOAR platform. The original raw event data remains, but is now complemented by this new wealth of information.
Leveraging Dynamic IOC Correlation
“Dynamic” IOC correlation is crucial. It means that the enrichment process is triggered in real-time, using the most up-to-date threat intelligence available via API, rather than relying on static, potentially outdated blocklists. When an alert arrives, the system queries the external world at that moment. If an IP was marked as malicious 30 seconds ago, the enrichment payload will reflect that, enabling analysts to make decisions based on current reality.
Operationalizing the Solution: SOAR Playbooks and Millisecond Responses
The true power of automated enrichment is realized when it is combined with automated response. Once an alert is enriched with high-fidelity, malicious context, the system shouldn’t just present it; it should take immediate, pre-approved action. This is the domain of SOAR playbooks.
Sample SOAR Workflow for Rapid Containment
Imagine a high-fidelity alert from an EDR tool: “Malicious process execution detected.”
- Ingestion: The SOAR ingests the alert.
- Enrichment: The playbook immediately extracts the associated process file hash and queries multiple threat intelligence APIs (e.g., VirusTotal and CrowdStrike).
- Condition: Within milliseconds, the APIs return with a unanimous verdict: “Malicious. Associated with known ransomware family X. Reputation score: 100/100.”
- Action Logic: The playbook, pre-approved for immediate action on specific high-confidence criteria, evaluates the enriched data.
- Automated Response: The playbook executes a series of actions within milliseconds:
- Containment: Commands are sent to the EDR agent to quarantine the compromised asset from the network, preventing lateral movement.
- Ticketing: An incident response ticket is automatically created in the ITSM tool (e.g., Jira or ServiceNow) and populated with the enriched alert payload.
- Notification: The relevant security and operations teams are immediately notified via email or Slack/Teams about the contained incident.
- Documentation: All automated actions taken are meticulously logged and appended to the incident ticket for auditing.
By executing these containment actions within milliseconds of detection, before an analyst even has a chance to view the alert, organizations can drastically limit the potential blast radius of an attack and prevent significant data loss or system disruption.
Architecting for Restricted Environments (GCC-High Enclaves)
Implementing these automated API integrations can be challenging in restricted or highly regulated environments, such as Government Community Cloud (GCC-High) enclaves. These environments often have stringent controls over outbound internet access, making direct API calls to external services difficult.
Architecting for these scenarios requires careful planning and the use of dedicated proxies and secure gateways:
- Dedicated Enrichment Proxies: Deploy dedicated, monitored proxy servers within the secure enclave. Configure the SIEM/SOAR system to route all external threat intelligence API requests only through these authorized proxies.
- Secure Gateways/API Aggregators: Utilize secure gateways (e.g., Akamai Edge, Cloudflare Spectrum) as intermediaries. These gateways can serve as aggregation points, terminating connections from the enclave’s proxies and initiating outbound requests to the desired threat intelligence APIs on their behalf. This provides an additional layer of control and logging.
- Strict Egress Controls: Implement Granular egress firewall rules, explicitly allowing outbound connections only to the authorized secure gateways or API endpoints, and only from the designated proxy servers.
- Logging and Auditing: Rigorously log all traffic passing through the proxies and gateways. Audit these logs regularly to ensure that external access is limited strictly to authorized enrichment activities and that no data leakage or unauthorized communication is occurring.
This architecture ensures that crucial enrichment data can be leveraged even within restricted environments, without compromising the security or compliance posture of the enclave.
Measuring Success and Ensuring Alignment with Frameworks
Implementing automated enrichment and response is a significant undertaking. Measuring its impact and ensuring alignment with established security frameworks is essential for validating the investment and demonstrating maturity.
The Reduction of Mean-Time-To-Detect (MTTD)
The primary metric for success should be the reduction of MTTD. This metric directly reflects the efficiency of the detection and validation process. Success can be measured by comparing pre-and post-implementation MTTD for key alert types and severity levels.
- Before: Time from EDR detection to manual validation by an analyst (minutes to hours).
- After (Validation): Time from alert ingestion to automatic validation based on enriched data (seconds).
While MTTD measures the time to detection, automated response actions (like asset quarantine) can also positively impact Mean Time To Respond (MTTR). Measuring both metrics provides a holistic view of SOC efficiency gains.
Audit Automated Response Actions to CISA Risk Reduction Frameworks
Automation must be implemented with care to avoid unintended negative consequences (e.g., quarantining a critical production server based on a false positive). All automated response actions must be meticulously audited and aligned with comprehensive risk management and risk reduction frameworks, such as those provided by the Cybersecurity and Infrastructure Security Agency (CISA).
- CISA Risk Reduction Framework Alignment: Mapping automated responses directly to CISA frameworks (e.g., “Critical Infrastructure Sectors,” “Risk Management Agency (RMA)”) can help organizations demonstrate that their automation strategy is purposeful and designed to protect critical assets and systems.
- Granular Approvals: Implement granular approval processes within the SOAR platform. Only authorize immediate, automated response actions for specific, high-fidelity criteria and a narrow scope of assets. Critical servers or applications should generally require manual approval before disruptive containment actions are taken.
- Comprehensive Auditing and Logging: Audit all automated actions taken. The audit trail must include:
- Timestamp: When the action was initiated and completed.
- Action Taken: Exactly what action was executed (e.g., “Isolated host [HOSTNAME]”).
- Triggering Criteria: The specific alert and enriched data that met the playbook’s condition for automated action.
- Approved By: If manual approval was required, who granted it.
- Output/Result: The result of the action (e.g., “Success/Failure” message from the target tool).
Regularly review these audit logs to identify any issues with automated playbooks, unintended side effects, or opportunities for refinement.
Conclusion
Automating contextual enrichment with dynamic IOC correlation and integrating it with SOAR playbooks is not a luxury; it’s a necessity for modern security operations. By shifting the burden of alert validation from human analysts to intelligent systems, organizations can drastically reduce false positives, prevent alert fatigue, and—most importantly—accelerate threat detection and containment.
Stop manually validating alerts. Implement an architecture that delivers enriched, actionable context within milliseconds, and configure SOAR playbooks to act decisively on that intelligence. By aligning these efforts with established risk reduction frameworks and measuring success by the reduction of MTTD, security teams can transform from being reactive responders to proactive defenders, better equipped to navigate the complexities of today’s threat landscape.
About the Author Sam Jobes, CISA-CISSP, is a 20-year information security veteran specializing in enterprise security architecture, GRC automation, and building scalable infosec programs for high-growth technology companies.