Enforcing Zero-Trust in CI/CD
The DevOps revolution promises unprecedented speed and agility, allowing organizations to ship software faster than ever before. Yet, this relentless drive for velocity often introduces significant friction: security bottlenecks. Traditional security models, built on perimeters and static check-gates, crumble under the pressure of dynamic, automated Continuous Integration and Continuous Deployment (CI/CD) pipelines. In today’s landscape of sophisticated supply chain compromises and ubiquitous containerization, “shifting left” is insufficient on its own.
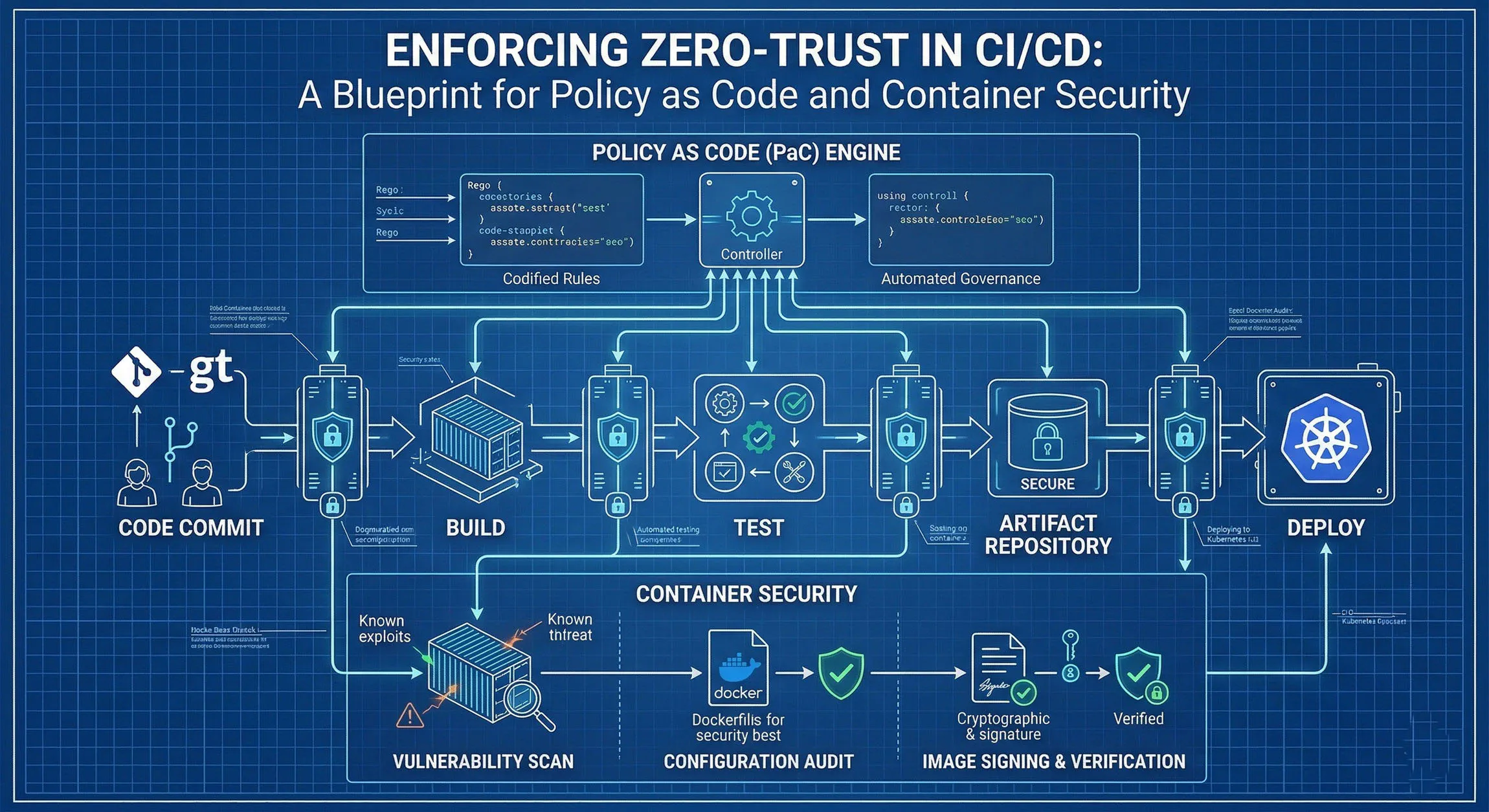
We need a new operating model for pipeline security. We need a model that doesn’t trust by default and continuously verifies every action, every identity, and every artifact. This is Zero-Trust Architecture (ZTA) applied to CI/CD, and its enforcement mechanism is the potent combination of Policy as Code (PaC) and Container Security.
Here is your blueprint for building a resilient, Zero-Trust pipeline.
Redefining Trust in the Pipeline
Zero Trust is a strategic mindset, not a peripheral product. Applied to CI/CD, it replaces implicit trust with explicit, continuous verification across three main vectors:
- Identity Verification: Never trust that a commit or deployment came from the authorized user or machine. Validate identities (humans, service accounts, runners) continuously using strong authentication and least-privilege access.
- Action Authorization: Do not assume a deployment is safe just because it passed a build step. Authorize every configuration change, secret access, and infrastructure modification based on dynamic, context-aware policies.
- Artifact Provenance and Integrity: Assume every dependency, base image, and compiled artifact is potentially compromised. Verify the origin (provenance) and integrity of every digital component throughout its lifecycle.
The Pillars of the Blueprint
A successful Zero-Trust CI/CD strategy requires integrating two powerful security disciplines directly into the automated workflow.
Pillar 1: Policy as Code (The Rules of Engagement)
Policy as Code is the practice of managing security, compliance, and operational rules using machine-readable definition files (code), rather than manual checklists or disconnected interfaces.
Codifying policies allows organizations to:
- Automate Enforcement: Integrate security gates directly into the CI/CD flow, allowing the pipeline to automatically test and block non-compliant changes without manual intervention.
- Ensure Consistency: Define a single security standard and enforce it uniformly across different clouds, environments (development, staging, production), and clusters.
- Version and Audit: Store policies in version control (Git), tracking who changed what, when, and why, providing a definitive audit trail for compliance.
- Provide Developer Feedback: Offer immediate, actionable feedback to developers directly within their workflows when a policy is violated (e.g., “Build failed: Image configuration violates Security Policy #14”).
A central Policy Engine ingests these codified rules and automatically evaluates pipeline actions and configurations against them, making instantaneous pass/fail decisions.
Pillar 2: Container Security (Protecting the Cargo)
Containers are the dominant artifact of modern delivery, but they present unique security challenges and opportunities. A Zero-Trust container strategy must protect the software from supply chain to runtime.
- Vulnerability Management: Scanning application code (SCA) and container images (OS and language dependencies) is critical. Zero Trust assumes vulnerabilities exist; security focuses on detecting and mitigating them before they can be exploited.
- Secure Configuration: Codifying secure defaults (e.g., denying root users, enforcing read-only root filesystems) prevents misconfigurations that attackers routinely exploit.
- Software Bill of Materials (SBOM): Generating a detailed inventory of every software component provides visibility and allows for rapid identification when new vulnerabilities are disclosed.
- Provenance and Trust: Signing images with cryptographic keys and verifying those signatures provides assurance that an image hasn’t been tampered with and originated from a trusted source.
The Integrated Blueprint for Zero-Trust CI/CD
The magic happens when you weave Zero-Trust principles, PaC, and Container Security into a cohesive, automated workflow within your CI/CD platform.
Phase 1: Preparation (Codifying Standards)
Before automating enforcement, you must define your organization’s standards as code.
- Define Security Policies: Translate your security, compliance, and best practices into human-readable policies (e.g., using a high-level declarative language).
- Examples: “Deny deployment of images with critical vulnerabilities,” “Force containers to run as non-root,” “A database cluster boundary must not allow direct inbound traffic from an external internet gateway,” “Require code signing and provenance for all production images.”
Phase 2: Build-Time Security (Verifying Inputs)
Focus on validating the components that build your application and infrastructure.
- Secure Code & Dependencies: Automatically scan code and dependencies (SCA) for vulnerabilities before images are built. Generate and verify SBOMs to maintain transparency.
- Secure Build Environments: Isolate build runners, ensuring they only have the minimal necessary permissions (least privilege). Use ephemeral environments to assume compromise.
- Scan Infrastructure-as-Code (IaC): Validate IaC definitions (e.g., Kubernetes manifests, Terraform plans) against your codified configuration policies before any resources are provisioned.
Phase 3: Supply Chain Validation (Policy Enforcement Gates)
This is the central enforcement point, where Policy as Code validates the artifacts created by the build process.
- Image Scanning: Integrate vulnerability scanners directly into the CI/CD pipeline after image creation.
- PaC Enforcement: The key step is evaluating the scan results and artifact configuration against your predefined policies.
- Example 1: If the vulnerability scanner finds critical vulnerabilities and your policy is set to “fail build on critical vulnerabilities,” the pipeline fails and blocks the deployment.
- Example 2: The Policy Engine checks the image configuration (Dockerfiles) to ensure non-root execution and security best practices. If it violates a rule (e.g., “Must not run as root”), the build fails.
Phase 4: Admission Control and Runtime Security (The Final Gate)
Zero-Trust continues even after deployment.
- Admission Control: The container orchestration platform (like Kubernetes) uses an admission controller to perform a final policy check at deployment time. It verifies image signatures and provenance (integrity/trust) and re-enforces configuration policies before accepting the deployment, ensuring that only validated, compliant artifacts are allowed to run.
- Runtime Monitoring: Zero Trust does not stop at deployment. Continuously monitor running containers for configuration drift, unexpected behavior, and new vulnerabilities, feeding back runtime intelligence to refine policies and improve pipeline security.
The Payoff: Resilience by Design
Implementing this integrated blueprint transforms the CI/CD pipeline from a point of vulnerability into a defensive asset. By combining Zero-Trust principles, the declarative power of Policy as Code, and the deep visibility of Container Security, you build resilience by design.
You move from a world where security is maintained by heroic manual effort and ad-hoc checks to a world where insecure actions are impossible by design. You gain speed, consistency, continuous compliance, and significantly reduce supply chain risk, empowering your DevOps teams to accelerate delivery while ensuring robust, verified security at every step.