The Paradigm Shift to Policy as Code
Manual security reviews bottleneck engineering velocity. Architects must embed security controls directly into the CI/CD pipeline. Policy as Code (PaC) automates governance, mapping technical configurations directly to regulatory mandates like ISO 27001 and NIST 800-53.
During my tenure executing enterprise architecture at AT&T, we learned that manual security gates fail at scale. Transitioning to PaC eliminated drift and established a verifiable audit trail for every infrastructure deployment.
Here is a comprehensive blog post based on your request.
Immutable Infrastructure
In the traditional, “mutable” world of IT infrastructure, servers are treated like pets. We give them unique names, we log in to fix them when they are sick, and over time, each one develops a unique personality (configuration drift) that makes reproducibility impossible. A quick patch here, a firewall tweak there, and suddenly, no one remembers exactly how the production server was configured. This is the origin of the “it works on my machine” problem when applied at scale.
If we want to build resilient, scalable, and secure applications in modern, multi-cloud environments, we must move away from treating servers like pets and start treating them like cattle.
This is the core tenet of Immutable Infrastructure.
Defining Immutable Infrastructure
Immutable Infrastructure is a paradigm where infrastructure components (virtual machines, containers, networks) are replaced rather than modified after they are deployed.
If you need to patch an application or update an OS configuration, you do not ssh into the running server to run apt-get update. Instead, you build a new, updated base image (a new “Golden Image”), test it, and then deploy it to replace the existing running instance.
The running components are read-only. Modification is forbidden.
The Benefits of Immutability
- Elimination of Configuration Drift: Every deployment starts from a known, tested, and version-controlled base image.
- Instant Rollbacks: If a deployment fails, you don’t need to debug the current state. You simply redeploy the previous Golden Image, which you know works.
- Reproducibility: You can recreate the exact production environment in staging or development instantly.
- Security by Design: Since running components are read-only, attackers cannot install persistent malware or tweak system configurations. Furthermore, “cattle” servers have much shorter lifespans, minimizing the time window a component is vulnerable to a newly discovered exploit.
The Multi-Cloud Compliance Nightmare
While immutability solves reproducibility and consistency problems, moving to a multi-cloud environment introduces a massive governance and compliance friction point.
Organizations use AWS, Azure, and GCP simultaneously to avoid vendor lock-in and exploit best-of-breed services. However, each cloud has its own APIs, its own IAM models, and its own configuration rules. How do you enforce a unified corporate policy-like “all storage buckets must be encrypted” or “no servers may have public SSH access”-when you have to implement that policy in AWS IAM, Azure RBAC, GCP Organization Policies, and Kubernetes network policies separately?
Relying on manual auditing or central cloud-native compliance tools (like AWS Config or Azure Policy) creates silos, fragmentation, and slow, reactive enforcement.
You cannot secure multi-cloud chaos with manual spreadsheets and reactive auditing. You need automated, proactive enforcement. You need Policy as Code.
Enter Policy as Code (PaC)
Policy as Code is the practice of codifying, versioning, and automating your compliance requirements using a declarative policy language rather than disconnected configuration interfaces.
Think of it as the “DevOps for Governance.” Instead of writing a text document that says “Encryption must be enabled,” you write a piece of code (often using a language like Rego, used by Open Policy Agent - OPA) that makes a dynamic decision based on input data.
The following codified requirement is stored in Git, versioned, pull-requested, and tested, exactly like application source code. The PaC approach provides a single, unified language (like OPA/Rego) that can be applied across all cloud providers and infrastructure types (IaC, Kubernetes, APIs).
Example logic:
If resource_type == "storage_bucket" AND attributes.encryption == false:
DECISION: DENY
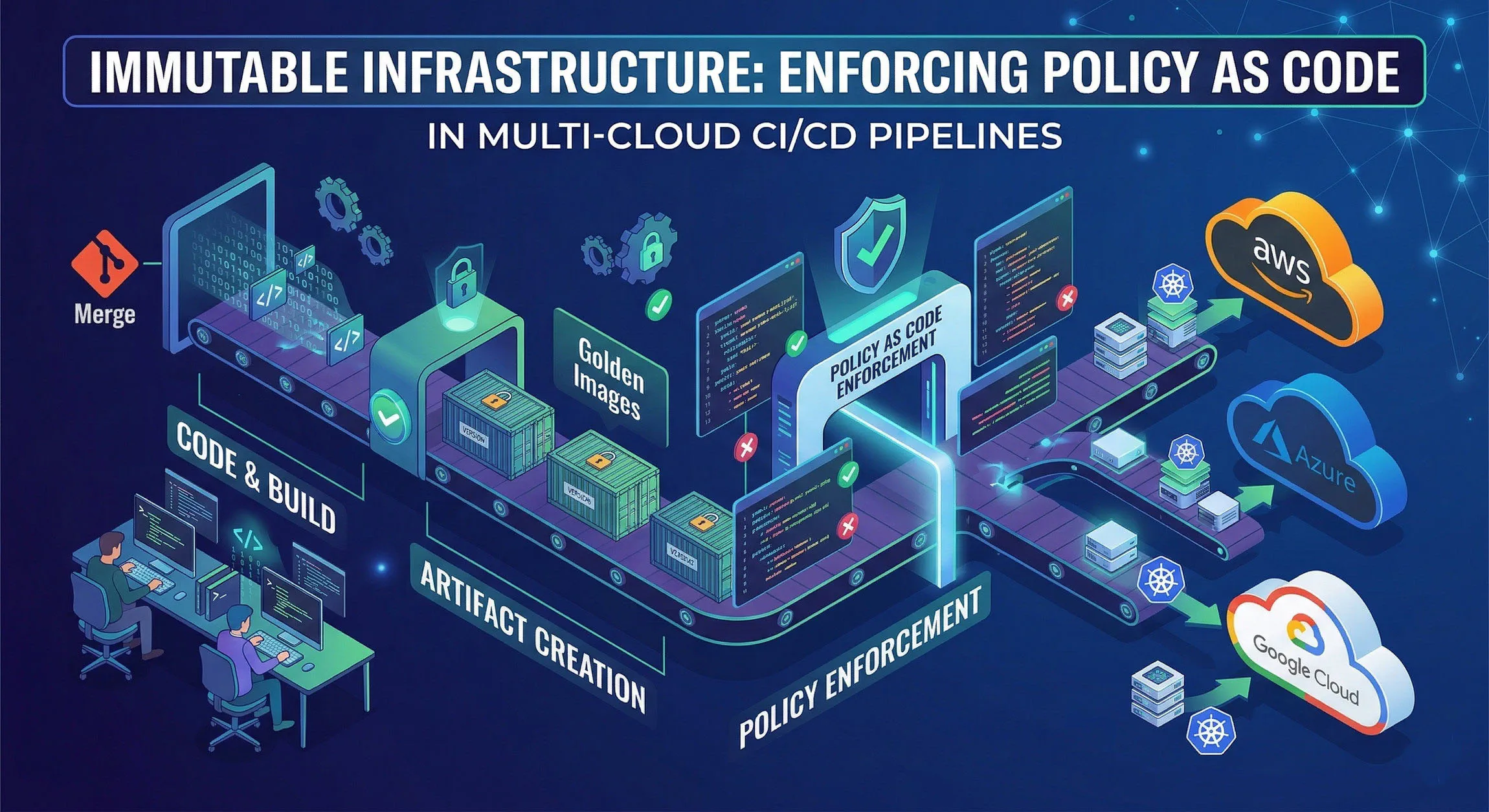
Blueprint: Unified Enforcement in the Multi-Cloud CI/CD Pipeline
The true power of Immutable Infrastructure and Policy as Code is realized when they are unified within the CI/CD Pipeline. This is where we facilitate DevSecOps and continuous enforcement, shifting governance left as early as possible in the development lifecycle.
Here is how you engineer a multi-cloud CI/CD pipeline that proactively enforces PaC on immutable artifacts.
Phase 1: Shift Left (Build & Plan Time)
Detection engineering starts before any resource is even provisioned.
The Golden Image Builder:
We start at the base. We do not manually provision VMs. We use tools like HashiCorp Packer to create hardened, immutable base OS images (AMI, Azure VHD, GCE Image). We define the security baseline as code (using Ansible or Shell scripts) that runs once during the image build process. This image is then tagged with a precise version number.
Infrastructure as Code (IaC) Scanning:
Developers define their intended multi-cloud infrastructure using standardized, machine-readable IaC definitions (e.g., Terraform or Crossplane).
When a developer commits their IaC, the CI/CD pipeline instantly runs it through a Policy Engine (like OPA/Rego). The pipeline does not run against a manual checklist; it runs the PaC code.
- Example Rule: A developer tries to use Terraform to create an Azure Storage Account that allows public anonymous access.
- Action: The Policy Engine evaluates the Terraform plan against the unified PaC rule. It finds a violation. The CI/CD pipeline fails, and the developer receives an error before the infrastructure is even built. The misconfiguration never proceeds further down the pipeline.
Phase 2: Continuously Integrate and Verify
In the multi-cloud world, continuous verification is not optional. We must prove the artifact is what we expect.
- Image Integrity Validation: When the new image is produced, its hash and configuration (SBOM) are verified against the predefined security standards.
- Policy Unit Testing: Just as we test application logic, we must write unit tests for our policy code. For example, a test must confirm that a policy correctly denies a non-compliant deployment plan. This ensures that changes to governance don’t accidentally weaken defenses.
Phase 3: Deployment Gatekeeper (Admission Control)
This is the crucial final enforcement point. Even if the IaC scan passes, we need a final “Admission Controller” gate at deployment time to ensure that what is actually being instantiated in production strictly matches the tested and versioned Golden Image.
Multi-Cloud Application Deployment:
The validated Golden Image is deployed to the various cloud environments via the CI/CD platform (e.g., Jenkins, GitHub Actions).
This is where the PaC engine acts as a dynamic admission controller for the entire platform. It translates abstract policy intent (e.g., “no unencrypted storage buckets”) into cloud-specific technical checks across AWS, Azure, GCP, and Kubernetes simultaneously.
- Admission Control Logic: For example, a SOAR playbook in the pipeline can call the PaC engine to validate that a proposed AWS S3 bucket policy (translated from the unified PaC rule) strictly matches the corporate standard before final approval.
Key Multi-Cloud Application:
The PaC language (Rego/OPA) remains constant. It doesn’t change based on whether you are deploying to AWS or GCP. The Policy Engine (operating as an admission controller) dynamically translates the unified rule into specific decisions for each CSP’s native RBAC and configuration requirements.
- Result: Only validated, compliant, and known-good immutable artifacts are allowed to execute. The pipeline guarantees that a non-compliant deployment is engineered to be impossible by design.
Conclusion
The shift to Immutable Infrastructure and Multi-Cloud environments is no longer a choice; it is a competitive necessity. But manual governance cannot secure modern chaos. Relying on disconnected native cloud tools for compliance is reactive, fragmented, and doomed to fail.
By combining the declarative simplicity of Zero Trust principles with the automated, multi-cloud declarative language of Policy as Code (Rego/OPA) and embedding that engine directly into the automated multi-cloud CI/CD workflow, you fundamentally transform your security posture. You move from a world where resilience is maintained by heroic manual effort and ad-hoc checklists to a world where resilience is maintained by design. You stop catching misconfigurations and start preventing them entirely. This unified approach mitigates complex compliance friction, reduces Mean Time to Remediate (MTTR), and provides continuous, provable assurance across your entire digital estate.