Metrics-Driven Security: Building Automated Reporting and Telemetry Health Checks
In today’s complex cyber threat landscape, having a sophisticated security architecture is just the starting point. The real challenge lies in ensuring that this architecture is functioning as intended, providing the desired level of visibility, and effectively reducing organizational risk. A purely reactive approach, which only addresses issues after a security incident or a system failure, is no longer sustainable.
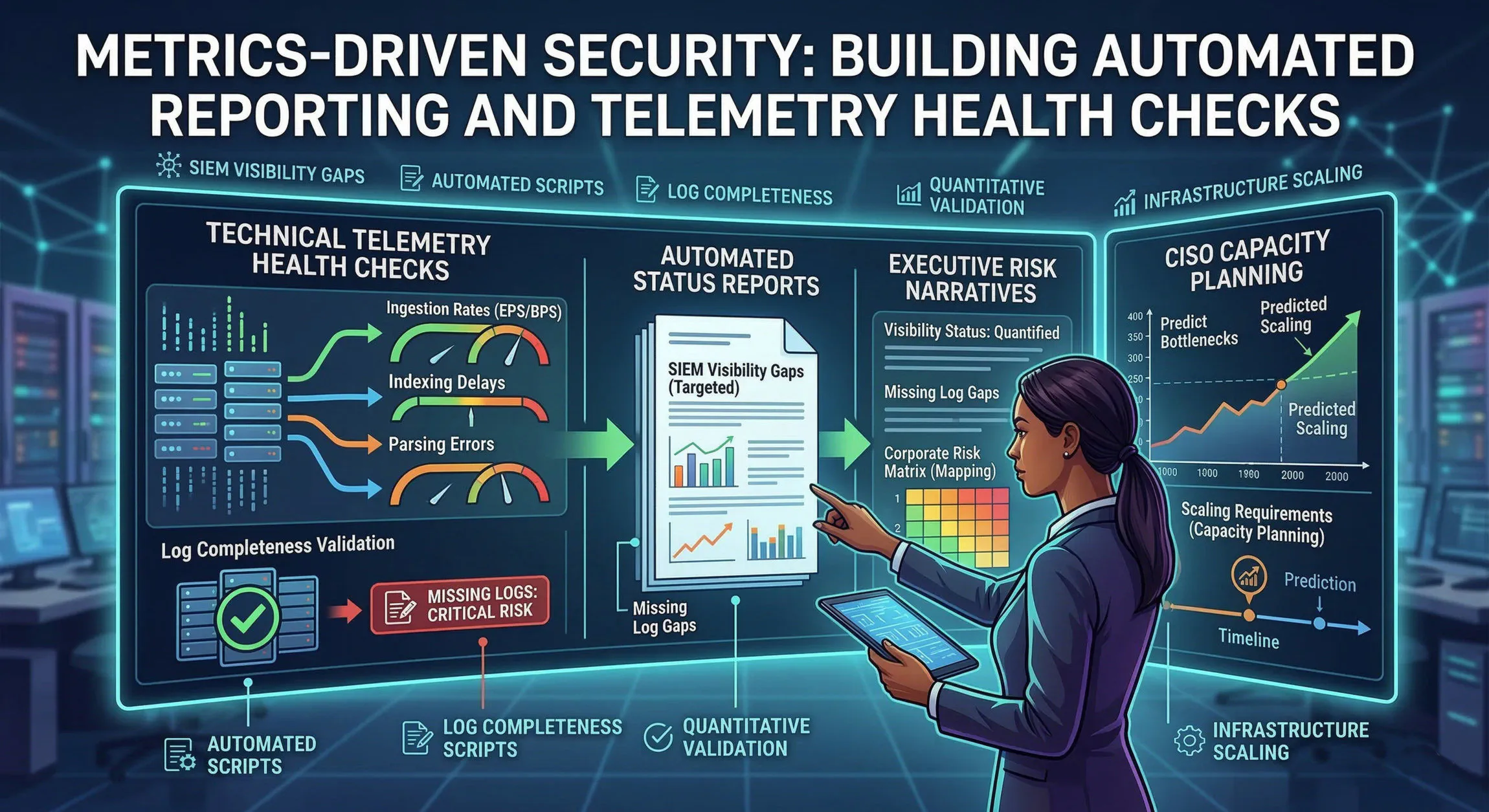
A proactive and efficient security posture demands a shift towards metrics-driven security—a model that uses quantitative data to validate the effectiveness of defensive controls and drive continuous improvement. This approach isn’t about collecting data for data’s sake; it’s about translating raw technical telemetry into actionable insights for both operational teams and executive leadership.
This blog article explores how to architect and implement the automated reporting and telemetry health checks necessary to build a truly metrics-driven security organization.
The Foundation of Visibility: Validating Telemetry Completeness
The most advanced SIEM with the best detection rules is useless if the logs it relies on are missing or incomplete. Automated validation of log telemetry from critical infrastructure is the first, and most important, step in building a metrics-driven security program.
The Risk of Missing Logs
Missing logs create critical blind spots where attackers can operate with impunity. An attacker might compromise a domain controller and clear its security logs to hide their tracks. Or, a critical firewall might misconfigure its logging rules after a firmware update, blinding security teams to external network attacks. In these scenarios, the absence of a security event is the primary indicator of a major problem.
Relying on manual spot-checks or purely reactive alerts for log delivery failures is insufficient. You need a proactive, automated mechanism to ensure that logs are being generated and received as expected from all critical data sources.
Automated Scripts for Log Completeness Validation
Build automated scripts to validate the completeness and integrity of log delivery chains. These scripts should target critical data sources such as domain controllers, firewalls, endpoints, web proxies, and authentication servers. The goal is to answer a fundamental question: “Am I seeing all the logs I should be seeing from my most important assets?”
These scripts can be engineered to perform a variety of checks:
- Log File Size and Event Count Monitoring: For systems that write to local log files, scripts can monitor file sizes and event counts over time. A sudden drop in file size or a significant deviation from historical event count baselines can indicate a logging problem. For event logs, scripts can query the number of security events generated in the last X minutes and compare it to established thresholds.
- Heartbeat and Communication Status Checks: Many log forwarding agents and collectors include built-in heartbeat mechanisms. Automated checks can monitor for missing heartbeats to detect when an agent has stopped communicating. For agents without heartbeats, scripts can perform basic network connectivity and service status checks on the logging endpoints.
- Detection of Log Gaps and Tampering: Advanced validation can involve cross-referencing log events. For example, a script could compare the events in a centralized log repository with those on a local system. Gaps in the centralized logs, or inconsistencies between local and remote records, could point to network packet loss, log tamper attempts, or data corruption in transit.
These validation checks ensure the telemetry foundation is robust and the visibility defined in your security architecture is actually operational.
Operationalizing SIEM Pipelines: Monitoring Ingestion and Processing
Once you have validated that the logs are leaving the source, you must monitor how they are handled within your centralized log processing and analysis system (SIEM). A robust SIEM pipeline must ingest, index, and parse data efficiently to ensure timely detection and response. This requires tracking key operational metrics.
Critical Operational Metrics for SIEM
Your metrics-driven security program should monitor these critical SIEM metrics:
- Ingestion Rates (EPS/BPS): Track Events Per Second (EPS) and Bytes Per Second (BPS) for each data source and for the system as a whole. Establish baselines for typical ingestion rates and configure automated alerts for unexpected surges or drops. A sudden, massive surge could indicate a misconfiguration or a denial-of-service attack, while a significant drop could indicate a log delivery failure or an ingestion bottleneck.
- Indexing Delays: Measure the time from an event’s generation on the source system to its indexing and availability for searching within the SIEM. Significant indexing delays degrade the speed of real-time detection and extend incident response times. Monitor this metric for critical log sources and establish acceptable thresholds.
- Parsing Errors and Unparsed Logs: Effective detection and automated response rules rely on well-structured, parsed data. Track the number and types of parsing errors encountered for different log sources. Also, monitor the volume of data that enters the SIEM but remains unparsed. These metrics point to visibility gaps and areas where parsing rules need to be updated or debugged.
By monitoring these operational metrics, security engineering teams can proactively identify performance bottlenecks, optimize ingestion pipelines, and improve the quality and utility of the data within their SIEM.
Translating Technical Metrics into Executive Risk Narratives
While detailed technical metrics are crucial for operational teams, they often fail to resonate with executive leadership. A key challenge of metrics-driven security is translating technical data into clear, concise risk narratives that align with business objectives and risk appetite.
Executives, including the CISO and board members, aren’t primarily concerned with EPS counts or indexing delays. They are concerned with questions like: “Are we adequately protected against top threats?”, “Is our security investment delivering value?”, and “How does our current posture map to our corporate risk matrix?”
The translation process is critical. Instead of reporting “a 15% drop in firewall log ingestion rates,” translate this metric into a risk narrative: “Degraded visibility into external network attacks has increased the risk of undetected network infiltration.” Instead of reporting “a 30-minute indexing delay for endpoint logs,” translate it to: “Delayed detection of compromised endpoints increases the potential impact of malware outbreaks and lateral movement.”
This approach connects operational metrics directly to business impact, moving the conversation from purely technical activities to strategic risk management.
Engineering Dashboards for Risk Matrices
A powerful tool for this translation is a custom dashboard that maps directly to your organization’s corporate risk matrix. This dashboard can aggregate various technical metrics and translate them into risk scores for specific areas of the business (e.g., identity security, data protection, network security). This provides CISOs with a high-level, real-time view of the organization’s security posture and risk levels, allowing them to make informed decisions and communicate more effectively with other executives and the board.
Strategic Reporting for CISO Empowerment and Capacity Planning
Metrics-driven security provides CISOs with the data they need to manage risk strategically and advocate for resources effectively.
CISO-Targeted Risk Dashboards
Executive risk dashboards should provide a concise, high-impact summary of overall security health and risk. Key components include:
- Overall Security Health Score: A composite score that aggregates various metrics to provide a single number representing the organization’s security posture.
- Mapping to Risk Appetite: A clear indication of how current risk levels compare to the organization’s established risk appetite and tolerance.
- Top Risk Drivers: A summary of the most significant risk factors, with the ability to drill down into the underlying technical data and automated narratives.
- Progress on Key Initiatives: A track of progress on security improvement projects, with data-driven evidence of their risk reduction impact.
This strategic dashboard empowers the CISO to move from being viewed as a purely technical leader to a strategic partner who can manage and communicate risk in a language the rest of the business understands.
Proactive Capacity Planning and Scaling
Perhaps the most significant strategic benefit of metrics-driven security is enabling proactive capacity planning. By monitoring historical ingestion rates (EPS/BPS), data retention times, and system resource utilization (e.g., CPU, storage, I/O), security teams can predict future infrastructure scaling requirements.
This allows them to:
- Predict Ingestion Bottlenecks Before They Occur: By analyzing trends in data volume growth, security teams can anticipate when ingestion or processing capacity will be exceeded and take proactive steps to scale up infrastructure.
- Optimize Infrastructure Costs: Quantitative data can be used to right-size infrastructure and avoid over-provisioning or under-provisioning resources.
- Ensure Continued Compliance: Proactive scaling ensures that logging and retention requirements can be met as data volumes grow, preventing compliance violations.
Conclusion
Metrics-driven security is not just about showing activity; it’s about proving the effectiveness of the defensive architecture. By building the necessary automated reporting and telemetry health checks, security organizations can shift from a reactive, fire-fighting mode to a proactive, evidence-based approach that delivers measurable value and effectively reduces organizational risk.
The journey towards metrics-driven security begins with validating the completeness and operational health of your telemetry foundation. It continues with monitoring the performance and utility of your SIEM pipelines. And it culminates in translating technical metrics into strategic risk narratives that empower security leaders to manage risk effectively and advocate for the resources they need to build a resilient and secure organization.
About the Author Sam Jobes, CISA-CISSP, is a 20-year information security veteran specializing in enterprise security architecture, GRC automation, and building scalable infosec programs for high-growth technology companies.