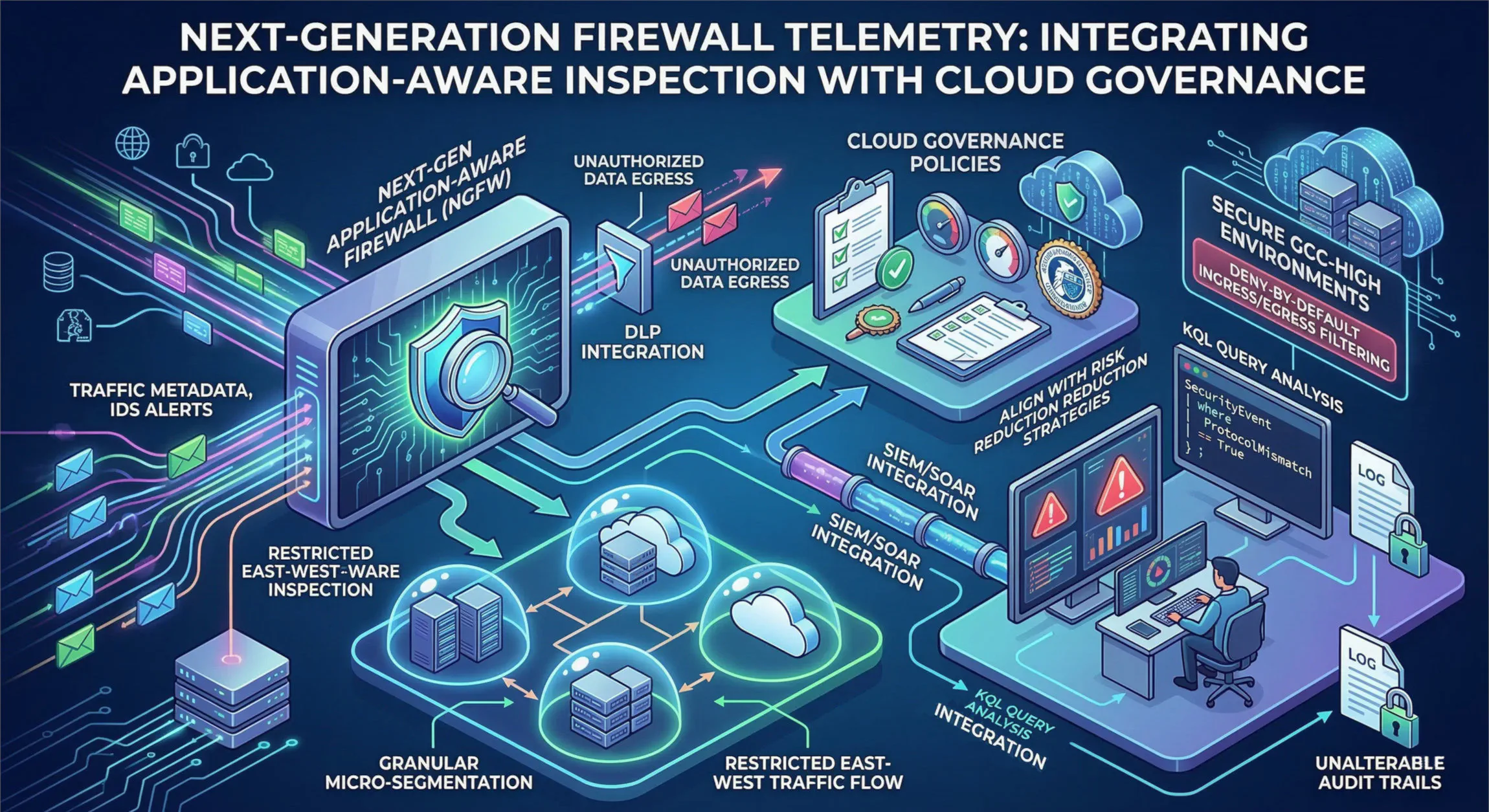
Next-Generation Firewall Telemetry: Integrating Application-Aware Inspection with Cloud Governance
Port-based firewall rules provide zero defensive value against modern adversaries. Threat actors routinely tunnel malicious payloads over port 443. Enterprise architecture demands Next-Generation Application-Aware firewalls equipped with inline TLS decryption capabilities. This article explores how to architect and implement these critical network security controls, integrating them seamlessly into a comprehensive Cloud Governance framework for a truly resilient defense.
The Inadequacy of Legacy Port-Based Rules
The days of assuming that traffic on port 80 is web browsing and traffic on port 443 is secure, encrypted web browsing are long gone. Attackers have weaponized this assumption, using standard, open ports to smuggle malicious traffic, command-and-control communications, and stolen data right past traditional network defenses. A legacy firewall rule that simply allows outbound TCP 443 to the internet is essentially an invitation for adversaries to operate unhindered within your network.
To combat this, enterprise security must evolve beyond simple port filtering and embrace Application-Aware inspection. Next-Generation Firewalls (NGFWs) provide deep visibility into the actual applications and protocols traversing the network, regardless of the port being used. This allows organizations to define granular policies that, for example, allow outbound access for specific approved SaaS applications (like Microsoft 365 or Salesforce) while explicitly blocking unapproved file-sharing services, malicious anonymizers, or P2P applications, even if they all attempt to tunnel traffic over port 443.
Inline TLS Decryption: The Critical Enabler
The vast majority of modern network traffic is encrypted using Transport Layer Security (TLS). While this is essential for data privacy, it also creates a massive blind spot for security teams. Without the ability to inspect the contents of encrypted traffic, NGFWs cannot effectively identify tunneled threats, detect malicious payloads, or prevent data exfiltration.
Inline TLS decryption is, therefore, a non-negotiable requirement for next-generation network defense. By deploying firewalls as transparent proxies with decryption capabilities, organizations can intercept and decrypt both inbound and outbound traffic, perform deep inspection on the contents, and then re-encrypt it before forwarding it to its final destination. This allows security tools to apply the full spectrum of defensive controls—including Intrusion Prevention Systems (IPS), malware analysis, and Data Loss Prevention (DLP)—to traffic that would otherwise remain hidden within the encrypted tunnel. Implementing this capability requires careful architectural planning, management of digital certificates, and a clear understanding of the privacy implications for different types of traffic.
Beyond Network Segmentation: Granular Micro-segmentation
While traditional network segmentation (e.g., using VLANs or subnets) helps logically separate different parts of the network, it often falls short in restricting east-west traffic within a segment, leaving critical workloads vulnerable to lateral movement. Micro-segmentation addresses this by applying granular network access controls down to the individual workload level, regardless of its location (on-premises or in the cloud).
Architecting for micro-segmentation involves deploying software-defined firewalls or distributed firewall agents that can enforce policies based on workload identity, application, or business context, rather than simple IP addresses and subnets. This approach isolates critical assets, restricts traffic flow between workloads to only what is strictly necessary for application functionality, and severely limits an attacker’s ability to move laterally within the environment after an initial compromise. Full-packet inspection (DPI) should be applied at micro-segmentation boundaries, just as it is at the perimeter gateways, to mitigate lateral movement threats that might originate from within the organization.
Mapping Network Controls to Cloud Governance Policies
Network access controls are most effective when they are directly mapped to and enforced by an overarching Cloud Governance framework. Cloud Governance defines the policies, processes, and controls that manage risk and ensure compliance across all cloud environments. Engineering choices must not only be technically sound but also aligned with formal risk reduction strategies and capable of withstanding rigorous CISA and CISSP-level compliance audits.
This integration requires security architects to translate high-level governance policies (e.g., “all outbound internet traffic must be inspected for malicious content” or “sensitive data must not leave authorized cloud boundaries”) into specific firewall configurations, rules, and telemetry. This ensures that network defenses are not arbitrary but are a direct implementation of the organization’s risk management strategy, providing quantifiable and audit-ready proof of compliance. native connection of DLP configurations at the gateway further strengthens this by intercepting unauthorized data egress directly at the point where it would attempt to leave the environment, directly supporting data loss prevention governance requirements.
Engineering Data-Driven Security Operations with Telemetry
The effectiveness of network defense is inherently tied to the visibility it provides. All firewall event data, intrusion detection alerts, and rich traffic metadata (including decrypted application-layer information) must be forwarded into central SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) pipelines. This creates a powerful dataset for threat hunting, incident response, and continuous monitoring.
Security operations teams can then use sophisticated analytical tools, such as Kusto Query Language (KQL), to analyze this telemetry at scale, identifying subtle indicators of compromise that would be missed by simple, isolated alerts. Analysts can investigate traffic spikes, protocol mismatches (e.g., non-compliant traffic over an approved application protocol), and beaconing behavior—common signatures of command-and-control communications. These data-driven insights are critical for proactively identifying and mitigating threats before they can cause significant damage. Furthermore, maintaining unalterable audit trails of all firewall activity and changes is non-negotiable for compliance validation, ensuring that security operations are transparent, auditable, and capable of withstanding rigorous scrutiny.
Securing Workloads in GCC-High Environments
Specific consideration must be given to securing workloads operating within highly regulated environments like GCC-High (Government Community Cloud - High). These environments demand exceptionally rigid security controls to protect sensitive government and defense data. In these contexts, network defense mechanisms must adhere to a strict deny-by-default posture for both ingress and egress filtering.
Ingress traffic must be limited to only necessary and pre-approved services, while egress filtering must strictly restrict outbound communication to only authorized and validated destinations. There is no room for implicit trust or broad, permissive rules in GCC-High architecture. Implementation of TLS decryption and native DLP integration at the gateway level becomes even more critical in these environments to ensure that all data movement is visible, inspected, and controlled, directly supporting the rigorous compliance mandates for protecting highly sensitive information.
Conclusion
The evolution from simple port-based rules to application-aware telemetry represents a fundamental shift in network security architecture. By integrating Next-Generation Firewalls with inline TLS decryption, granular micro-segmentation, native DLP, and a robust Cloud Governance framework, organizations can build a resilient defense capable of withstanding modern, sophisticated threats. The strategic use of telemetry in SIEM/SOAR pipelines enables data-driven security operations, while alignment with formal risk reduction strategies ensures that engineering choices are both effective and compliant. In an era of persistent and complex cyber threats, this comprehensive, integrated, and application-aware approach to network security is not merely a best practice; it is a critical imperative for ensuring the security, compliance, and operational integrity of the modern enterprise.
About the Author Sam Jobes, CISA-CISSP, is a 20-year information security veteran specializing in enterprise security architecture, GRC automation, and building scalable infosec programs for high-growth technology companies.