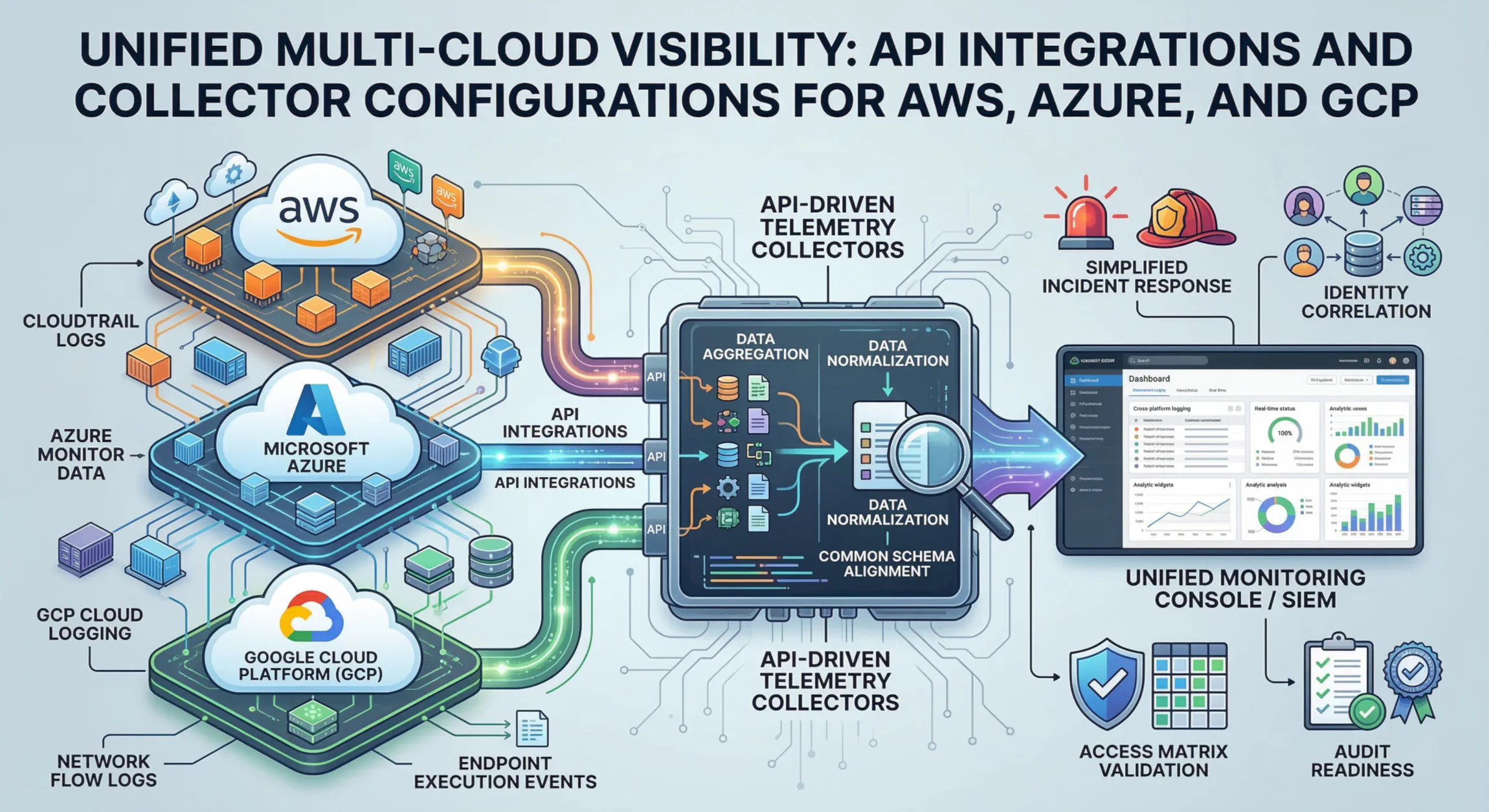
Unified Multi-Cloud Visibility: API Integrations and Collector Configurations for AWS, Azure, and GCP
Modern enterprise infrastructure is increasingly multi-cloud, leveraging the unique strengths of AWS, Microsoft Azure, and Google Cloud Platform (GCP). This distributed model, while powerful, introduces a profound challenge: visibility.
Traditional legacy security agents were designed for a static, pre-provisioned world. They struggle and often fail in the ephemeral, elastic, and API-driven environment of the modern cloud. In this context, visibility must be API-native. Your security team must design and configure API-driven telemetry collectors to gain a unified view across all cloud endpoints, services, and networks.
A unified multi-cloud visibility architecture aggregates diverse telemetry streams, normalizes them, and centralizes them for efficient analysis.
Let’s delve into the technical design and configuration of telemetry collectors for the major cloud providers.
Understanding the Need for API-Native Visibility
Legacy security agents present several fatal flaws in multi-cloud:
- Ephemerality: Agents cannot be deployed fast enough on instances that spin up for minutes or hours.
- Blind Spots: Agents can only monitor the operating system they are installed on. They have zero visibility into cloud-native services like serverless functions (Lambda/Functions/Cloud Functions), managed databases (RDS/CosmosDB/Cloud SQL), or networking services.
- Operational Overhead: Managing, patching, and updating agents across thousands of multi-vendor instances is an administrative nightmare.
API-driven collectors, conversely, fetch data directly from the cloud control plane. They ingest logs from management and data services, giving you visibility into all actions—including those by serverless functions and on managed infrastructure. This approach is elastic, scalable, and agentless.
Core Telemetry Sources: Management Logs
To build this visibility, you must tap into the management and data plane logs of each cloud provider.
AWS: CloudTrail
AWS CloudTrail is the bedrock of multi-cloud visibility for Amazon Web Services. It records all API calls, including the identity of the API caller, the time of the call, and the response from the service. Configuring a CloudTrail for cross-account or organizational visibility is the first step.
The most scalable way to ingest CloudTrail is not polling the API directly. Instead, configure CloudTrail to deliver logs to an S3 bucket and then use S3 event notifications to trigger an ingestion pipeline, such as AWS Lambda, which pushes the logs to your centralized SIEM or Data Lake.
Microsoft Azure: Azure Monitor
Azure Monitor is the centralized telemetry hub for Azure. It consumes metrics, logs, and traces. To get management-level logs, you must configure a “Diagnostic setting” on resources to stream activity logs to a specific destination, such as an Azure Event Hubs instance. Your centralized log collector can then ingest from this Event Hub.
GCP: Cloud Logging
Google Cloud Logging is a fully managed service that allows you to store, search, and analyze logs. GCP uses “log sinks” to route logs. To export logs outside of GCP to a central destination, create a sink with an export to either a Cloud Storage bucket or a Pub/Sub topic, which can then be subscribed to by your external collector.
Aggregating Network Flow Logs and Endpoint Events
Visibility is incomplete without deep network and endpoint introspection. Unified collectors must also ingest:
- Cloud Network Flow Logs: This includes AWS VPC Flow Logs, Azure NSG Flow Logs, and GCP VPC Flow Logs. Collecting these provides visibility into network conversations—source/destination IP, port, and protocol—crucial for identifying lateral movement.
- Endpoint Execution Events: This is where agents still provide value. For critical VMs or on-premises servers, EDR (Endpoint Detection and Response) agents must continue to send process execution events to your normalized pipeline. The architecture must accommodate this, feeding normalized agent telemetry alongside normalized API logs.
The Crucial Step: Data Normalization and Schema Alignment
Ingesting raw JSON logs is only 20% of the effort. The real work begins with normalization. An IpAddress field from CloudTrail will have a completely different name than a field from Azure Monitor or an EDR agent.
You must choose or design a common, flat, and scalable schema (e.g., Elastic Common Schema (ECS), Apache Parquet with a specific columnar definition, or OSSEM). Your collectors, such as AWS Lambda or Azure Functions, must parse each incoming log type, map its fields to the common schema, and output a normalized, JSON-LSD (Line-Separated JSON) format before centralization.
Unifying Visibility for Incident Response and Audit Readiness
Normalized, centralized logging simplifies everything.
- Unified Cross-Platform Analysis: In an incident response scenario, an analyst can perform a single query to see a user’s action across AWS and GCP, rather than logging into two separate consoles with different query languages.
- Access Matrix Validation: Correlate identity metrics (who is logged in) with infrastructure events (what they did) to validate that your IAM policies and access control matrices are being enforced correctly across all clouds.
- Audit Readiness: Regulators are increasingly demanding proof of audit readiness. Proper collector configuration and a normalized, historical log of all multi-cloud actions guarantee that your infrastructure satisfies strict regulatory frameworks (e.g., NIST, ISO 27001).
Design for elasticity and scalability from day one. Proper telemetry collector configuration is not a post-deployment consideration; it is a critical security prerequisite for all modern multi-cloud architectures.
About the Author Sam Jobes, CISA-CISSP, is a 20-year information security veteran specializing in enterprise security architecture, GRC automation, and building scalable infosec programs for high-growth technology companies.