Engineering Audit-Ready Threat Detection
Every Security Operations Center (SOC) manager knows the feeling. The auditor has arrived, and they have questions about detection logic, log coverage, and incident response timelines. The stress of compiling these reports often rivals the stress of an actual incident.
Traditionally, threat detection and compliance have been parallel efforts that rarely meet. The SOC focuses on technical metrics (events per second, mean time to respond), while Governance, Risk, and Compliance (GRC) teams focus on regulatory frameworks, control mappings, and risk registers. This disconnect creates gaps: security teams might spend weeks engineering detections for a threat that is not identified as a business risk, while critical enterprise risks remain uncovered by operational monitoring.
To survive an audit and-more importantly-to build a truly resilient organization, we must move past this siloed approach. We must engineer audit-ready threat detection that is directly integrated with risk management.
Defining ‘Audit-Ready’ Engineering
“Audit-ready” doesn’t mean scrambling for weeks before an annual check-up. It means having a demonstrable, repeatable system where compliance is a natural byproduct of good operations.
An audit-ready threat detection program can instantly answer these questions:
- Scope: Why are we collecting these specific logs and not others? (Answer: Because they monitor our critical assets.)
- Logic: Why did we deploy these specific detection rules? (Answer: Because they detect the top risks identified in our register.)
- Process: Can you prove your playbooks were executed correctly? (Answer: Yes, here is the automated, immutable audit trail.)
This requires engineering, not just deployment. It requires a fundamental shift to a risk-based strategy.
The Disconnect: The Threat vs. The Risk
To bridge the gap, we must understand why the current operational divide exists.
| Operational SOC | Business GRC |
|---|---|
| Focus: Technical Threats (Malware, Exploits, ATPs) | Focus: Business Risks (Data Breach, Service Outage, Compliance Fines) |
| — | — |
| Language: CVEs, TTPs, Indicators | Language: Impact, Probability, Criticality |
| — | — |
| Metric: Efficiency (MTTR) | Metric: Posture (Compliance Score) |
| — | — |
When a SIEM fires an alert, it’s often about a threat-for instance, “Brute force login detected.” However, without risk context, the SOC does not know if this is a script kiddie hitting a public web server with no valuable data (low business risk) or an attacker targeting a domain controller (high business risk).
Engineered detection maps technical threats back to business risk.
The Blueprint: Integrating the Stack with Governance
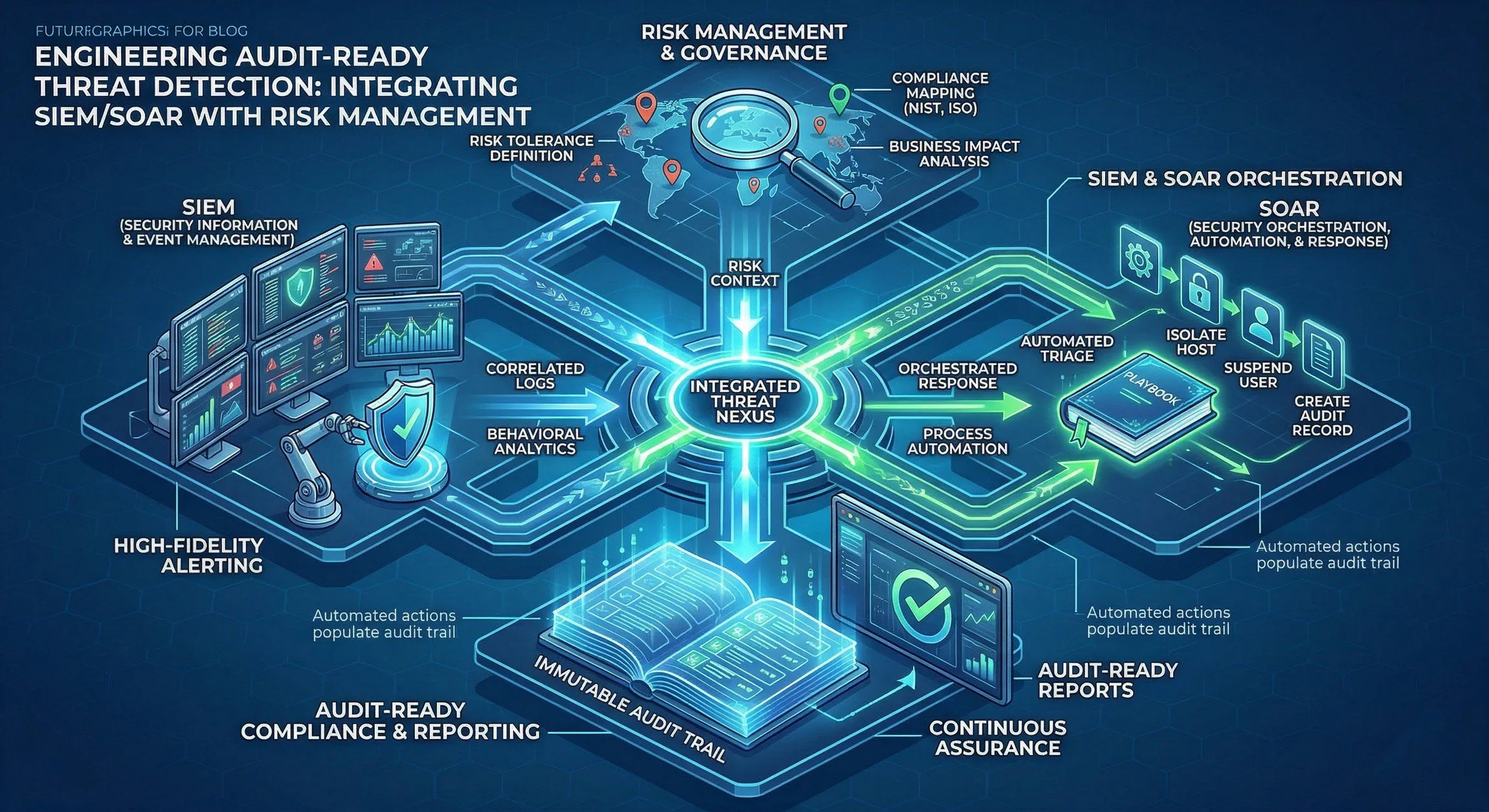
The following diagram illustrates how the technical components (SIEM/SOAR) are integrated bidirectionally with the governance and risk layers. This continuous loop ensures that operational security is always prioritized by enterprise risk.
The blueprint outlines a four-step process for integration.
Step 1: Identify and Contextualize Critical Assets
Detection engineering begins with knowing what to protect. GRC teams maintain the asset and configuration management database (CMDB), which identifies critical business assets (e.g., PII data stores, financial systems, public-facing applications).
This context must be ingested by the SIEM. A “Brute Force Login” alert should be dynamically scored by the business value of the target asset. If it’s targeting a development server with dummy data, it’s a low priority; if it’s hitting the customer data repository, it should instantly be elevated to a critical incident. This is context-aware detection.
Step 2: Define and Formalize Business Risks
The Enterprise Risk Register is the definitive list of what keeps the C-suite awake at night. This register typically includes risks such as:
- Ransomware causing prolonged service downtime (Business Interruption Risk).
- Insider threat exfiltrating critical Intellectual Property (Data Exfiltration Risk).
- Misconfiguration leading to public exposure of customer data (Compliance/Reputational Risk).
These high-level risks are the business language. To make them technical language, we must map them to specific attacker behaviors.
Step 3: Map Risks to Attacker TTPs (Threat Modeling)
This is the central engineering task. GRC’s risks must be mapped to operational reality. We do this by threat modeling, using frameworks like MITRE ATT&CK to identify the specific Tactic, Techniques, and Procedures (TTPs) that would realize a business risk.
Example 1: Ransomware Risk. The technical translation might be detecting TTPs like Data Encrypted for Impact (T1486) or Service Stop (T1489) on critical file servers.
Example 4: Insider Threat IP Theft Risk. This requires detecting unusual behaviors, such as Archive via Utility (T1560) on sensitive file shares or Exfiltration Over C2 Channel (T1041).
By connecting these three points (Critical Asset $\rightarrow$ Business Risk $\rightarrow$ Attacker TTP), you are engineering a high-fidelity, risk-based detection strategy. Auditors will love this clear line of sight, which proves that your monitoring is direct and efficient, focusing on what matters.
Step 4: Automate Response and Document Process
Audit failure is rarely about a missing alert; it’s about a failed or undocumented process. Auditors must see that your playbooks were executed correctly and consistently.
This is where SOAR shines. SOAR platform playbooks are orchestrated to execute repetitive triage steps and containment actions automatically. These are not just efficient; they are audit trails. Every action taken by a SOAR bot (isolating a host, disabling an account, querying threat intel) is automatically logged in an immutable ledger. These detailed case notes are evidence, demonstrating process compliance with incredible detail.
A mature integration loop goes further, feeding data back up: “Our engineered playbooks for containing IP theft risk have reduced containment time from four hours to five minutes.” This is the metrics that auditors, executives, and directors want to see.
Continuous Assurance: The Path to Maturity
Mature integration loop connects technical controls to governance.
- Risk $\rightarrow$ Detection: New high-level business risks automatically trigger a detection engineering sprint to cover them with technical monitoring.
- Compliance $\rightarrow$ Playbook: Changes in regulatory requirements (e.g., new state breach notification laws) are automatically reflected in updated SOAR playbooks.
- Detection $\rightarrow$ Risk: New detection capabilities or persistent false positives are used to refine the Enterprise Risk Register, improving risk scoring.
Survival of the Fittest
Audits do not have to be painful. The stress is not caused by the auditor’s questions, but by the difficulty of retrieving the answers. By engineering an audit-ready threat detection program that integrates your technical stack (SIEM/SOAR) with risk management (GRC), you create a demonstrable, efficient, and cohesive strategy. This transformation from a disconnected, “detect everything” approach to a focused, risk-aware strategy reduces attack impact, slashes MTTR, and makes continuous compliance a demonstrably provable reality.