Operationalizing Network Telemetry: Threat Hunting Across Disparate VPN and SDWAN Topologies
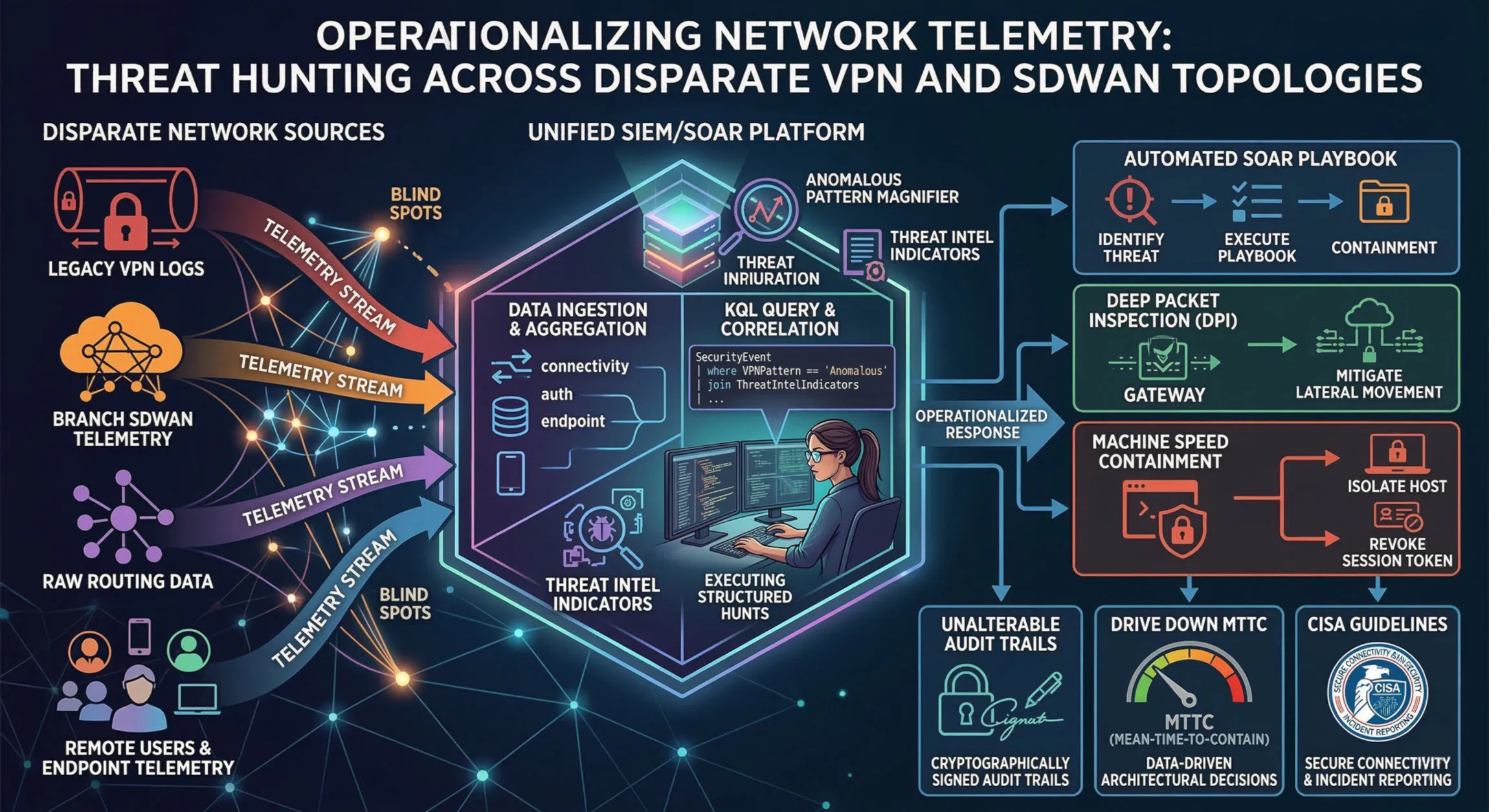
Network visibility dictates incident response efficacy. This fundamental tenet of cybersecurity architecture is increasingly strained in modern hybrid environments. The reality of most enterprises involves a messy patchwork of connectivity solutions: legacy client-to-site VPN concentrators, site-to-site tunnels connecting branch offices, multi-cloud SDWAN overlays, and raw on-premises routing infrastructure.
This disparity in network technologies creates dangerous visibility gaps. Disparate VPN logs, SDWAN telemetry, and raw routing data lack a common schema, making correlation difficult. Threat actors, well-aware of these “blind spots,” exploit them to establish persistence, move laterally, and exfiltrate data undetected. To counter this, organizations must move from passive logging to active, operationalized network telemetry.
Here is a technically in-depth blueprint for centralizing aggregation, executing structured threat hunts, and automating containment in complex network topologies.
Phase 1: Immediate Centralization of Log Aggregation
You cannot hunt what you cannot see. The first, and most critical, operational step is the immediate centralization of all relevant network and identity-based log data into a unified SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) platform.
Standardizing the Schema (The Normalization Challenge)
Simple ingestion is not enough. Raw Syslog data from a Cisco ASA, API telemetry from a Palo Alto Prisma SDWAN, and NetFlow from a core switch must be normalized into a common schema. Without a standard schema—like the Elastic Common Schema (ECS) or Splunk’s Common Information Model (CIM)—cross-platform queries become impossible.
Critical Telemetry Sources for Ingestion
A holistic network threat hunt requires the following data streams to be ingested and normalized:
- Connectivity Events (VPN & SDWAN): Ingest raw connection logs (Session Start/End, bytes transferred, duration, assigned IP, protocol). SDWAN telemetry must include overlay tunnel status and control plane messaging.
- Authentication Logs (Identity): VPN/SDWAN authentication logs must be tightly coupled with the connectivity events. You need to know not just that
192.168.10.50connected, but that it was userjane.doe@example.comwho authenticated via the Azure AD IDP. - Endpoint Telemetry: EDR (Endpoint Detection and Response) data from the connecting host is the necessary context to complete the picture. It allows correlation between a network connection (seen by the VPN) and the specific process on the machine that initiated it.
Phase 2: Executing Structured Threat Hunts via KQL
Once the data is normalized and centralized, security operations can shift from reactive alert-handling to proactive threat hunting. This involves constructing hypotheses and querying the unified dataset, often using powerful query languages like KQL (Kusto Query Language), to look for anomalous traffic patterns.
Hunting for Impossible Travel and Session Anomalies
One high-fidelity hunt involves correlating VPN/SDWAN authentication geolocation data. Threat actors with compromised credentials often log in from geographies inconsistent with the user’s known location.
// Hunting for Impossible Travel between VPN Sessions
SigninLogs
| where AppDisplayName == "Example Corporate VPN" or ServicePrincipalName == "SDWAN-Controller-App"
| project TimeGenerated, UserPrincipalName, Location, IPAddress, CorrelationId
| sort by UserPrincipalName, TimeGenerated desc
| serialize
| extend PrevTime = prev(TimeGenerated), PrevLocation = prev(Location), PrevIP = prev(IPAddress)
| where UserPrincipalName == prev(UserPrincipalName)
| extend TimeDiffSeconds = datetime_diff('second', TimeGenerated, PrevTime)
| extend LocationChanged = iff(Location != PrevLocation, true, false)
| where TimeDiffSeconds < 3600 and LocationChanged == true // Location changed within one hour
| project TimeGenerated, UserPrincipalName, Location, PrevLocation, IPAddress, PrevIP, TimeDiffSeconds
Correlating Anonymous Proxies and TOR Geolocation Authentications
Threat actors leverage anonymous proxies and the TOR network to obscure their source attribution. Hunting for VPN/SDWAN authentications originating from known TOR exit nodes or commercial proxy IP ranges is highly effective. Correlate this against known threat intelligence indicators.
Identifying Beaconing and Protocol Mismatches via Traffic Metadata
Query traffic metadata (NetFlow/IPFIX) to identify beaconing behavior, which is characteristic of C2 (Command and Control) traffic. Look for regular, low-volume “heartbeat” connections from internal hosts to unusual external IPs over allowed protocols (like HTTPS or DNS). Furthermore, analyze traffic metadata to identify protocol mismatches—for example, anomalous non-HTTP traffic attempting to traverse a web proxy port.
Phase 3: Mitigating Lateral Movement with DPI and Granular Micro-segmentation
Detection is only valuable if it leads to mitigation. While VPNs and SDWAN secure traffic “in transit,” they do not inherently protect against an attacker who has already established a beachhead inside the network perimeter. The traditional model of network-level trust is insufficient.
Deployment of DPI at the Perimeter and Branch Gateways
Implement full-packet inspection (DPI) at all key ingress and egress points, including branch SDWAN gateways and internet edge firewalls. Simple port and protocol filtering are easily bypassed. DPI analyzes the payload of packets, enabling the detection of malicious activity within seemingly legitimate application streams, such as SQL injection attempts or ransomware communication over DNS tunnels.
Deploying Identity-Aware Micro-segmentation
Attackers rely on the ability to move laterally between systems on the same network segment. Deploy granular micro-segmentation policies based on workload identity and user identity, not just IP addresses. If Jane Doe in Finance is accessing a SaaS accounting application via VPN, her device should be restricted from initiating a direct network connection to an R&D build server, even if they are on the same logical segment.
Phase 4: Driving Down MTTC with Automated Containment via SOAR Playbooks
In network-based incidents, containment speed is critical. Manual response times measured in minutes or hours are unacceptably slow. Threat hunters and incident responders must leverage SOAR playbooks to execute incident containment protocols automatically and at machine speed upon high-confidence detections.
Executing Automated Remediation Actions
When a hunt or a high-confidence alert indicates a compromised session, the SOAR platform should automatically execute a multi-step containment playbook, often interfacing directly with the identity provider (IDP) and the endpoint itself:
- Isolate Compromised Host: Send an isolation command to the EDR agent on the host to sever its network connectivity, leaving only a management channel for forensics.
- Revoke Session Tokens: Interface with the IDP (e.g., Azure AD or Okta) to revoke all active refresh and access tokens for the user account associated with the anomaly. This forces immediate re-authentication, which the attacker cannot perform without hardware-backed MFA (Multifactor Authentication).
By automating these steps, organizations can drive the mean-time-to-contain (MTTC) from hours down to milliseconds, effectively neutralizing compromised sessions before significant damage occurs.
Phase 5: Gaining Auditable Compliance and Strategic Capacity Planning
Finally, operationalizing network telemetry is not just a defensive tactic; it is necessary for maintaining compliance and audit readiness under strict regulatory frameworks.
Network engineers and incident responders must operate from a single source of truth—the centralized SIEM/SOAR. This unified data ensures consistency in data interpretation and accelerates cross-functional collaboration during a crisis.
Adhering to CISA Guidelines and Audit Requirements
Strictly adhere to CISA (Cybersecurity and Infrastructure Security Agency) guidelines for secure connectivity and incident reporting. Ensure the network security architecture provides unalterable, cryptographically signed audit trails of all access requests, policy decisions, authentication events, and security detections. In many GCC-High environments, these rigid, deny-by-default audit trails are non-negotiable for compliance validation (e.g., against NIST 800-171 or CMMC controls).
Ultimately, data-driven security operations provide the strategic insights needed to optimize overall security posture. By analyzing patterns of anomalies and legitimate traffic, organizations can make proactive architectural decisions, predicting infrastructure scaling requirements (e.g., VPN/SDWAN concentrator capacity) before ingestion bottlenecks or performance degradation can occur. A proactive threat hunting methodology, powered by operationalized network telemetry, is the key to building a resilient, defensible enterprise network in a complex hybrid environment.
About the Author Sam Jobes, CISA-CISSP, is a 20-year information security veteran specializing in enterprise security architecture, GRC automation, and building scalable infosec programs for high-growth technology companies.