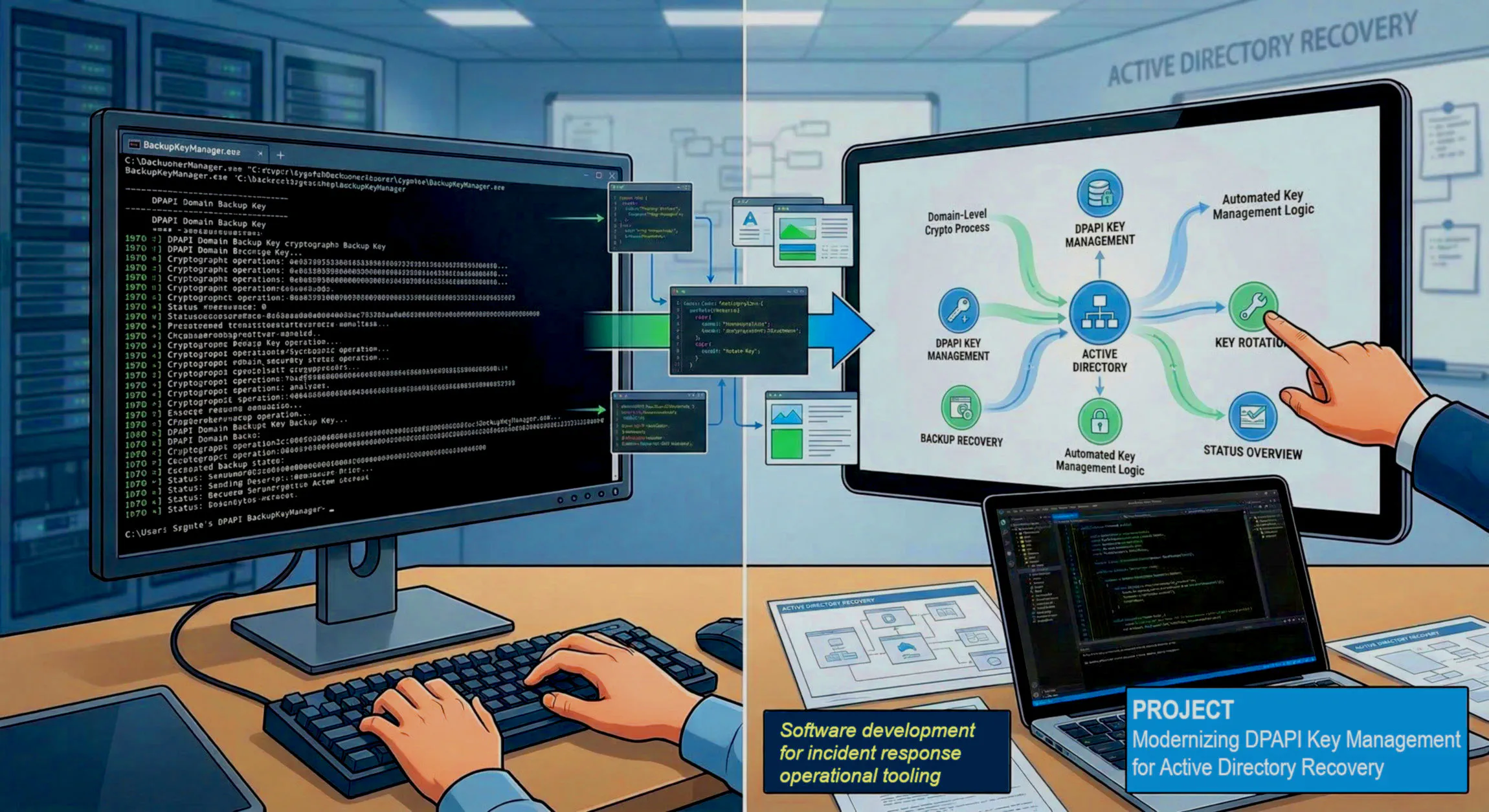
The Challenge: Cryptographic Persistence in Active Directory
During an Active Directory compromise recovery, rotating the DPAPI Domain Backup Key is a critical, yet often overlooked, remediation step. Because this key is permanent by default, an exposed key allows an adversary to decrypt user master keys domain-wide, indefinitely.
While Sygnia’s BackupKeyManager provides the necessary cryptographic logic to rotate these keys, its command-line interface requires high precision during a high-stakes incident.
The Solution: Architecting a “Low-Friction” Recovery Console
I designed and developed a Windows GUI Frontend for the BackupKeyManager utility to serve as a thin, validated operator console. The goal was not to replace the original research, but to operationalize it for rapid, error-free deployment in complex environments.
Key Performance Capabilities
- Validated Workflow Support: Direct implementation of
GetPublicKey,GenerateNewBackupKey, andValidateoperations. - Input Hardening: Built-in validation for Domain Controller FQDNs and GUIDs to prevent command syntax errors during crisis remediation.
- Integrated Telemetry: Real-time capture and display of CLI output, allowing responders to review AD object modifications without switching contexts.
Architectural Philosophy: “Wrapper, Not Fork”
One of the core design decisions was to maintain a strict separation between the UI Logic and the Cryptographic Logic. By acting as a wrapper, the application preserves compatibility with Sygnia’s original utility while providing a modern interface that enhances responder confidence.
Impact Metric: Reducing the “Margin for Error”
In security engineering, a technically correct tool is useless if it is operationally difficult to execute. This project demonstrates how thoughtful interface design can bridge the gap between technical research and frontline incident response.
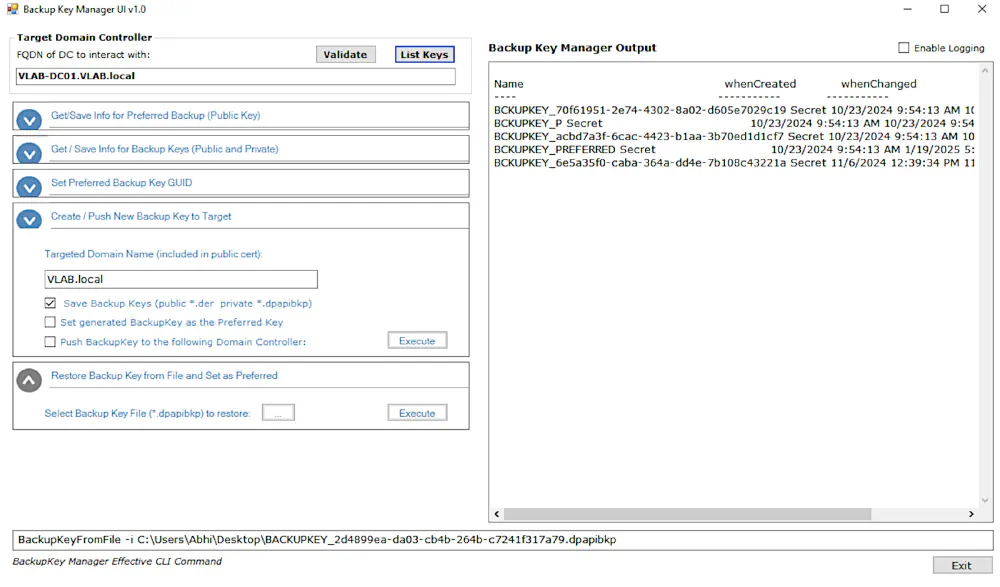
What the GUI Does
The application is built as a C# WinForms frontend for the original BackupKeyManager.exe. The interface collects the required operator inputs, builds the appropriate command-line arguments, launches the underlying executable, and displays the output back in the application.
The GUI supports the main workflows exposed by the underlying tool, including:
- retrieving the currently served public backup key
- retrieving and analyzing the active backup key
- generating a new backup key
- setting a preferred backup key
- validating the current configuration
- loading a backup key from file
I also added functionality to help enumerate existing backup key objects in Active Directory, making it easier to inspect key history and understand the state of the environment before making changes.
Practical Benefits
From an operations standpoint, the GUI helps by making the workflow more deliberate and readable.
Instead of requiring the operator to remember or reconstruct command syntax, the application presents the major actions in a structured way. Parameters such as domain controller, FQDN, GUID, and file input can be entered directly through the interface. Output from the CLI is returned to the user in the same session, which makes it easier to review actions and results without switching contexts.
For security teams, that matters. During remediation work, even small usability improvements can reduce mistakes and improve confidence in the execution of a sensitive procedure.
Summary
This project sits at the intersection of security engineering and usability. It does not attempt to replace the original tool or its research. Instead, it aims to make an important defensive capability easier to use in practice.
For me, that is part of what makes security engineering valuable: not only understanding the underlying problem, but also building practical tools that help people solve it more effectively.
Attribution
This project is a frontend built to work with Sygnia’s BackupKeyManager on GitHub. Full credit for the original research and the underlying DPAPI backup key management utility belongs to Sygnia. Their work on the exposure and rotation of the DPAPI Domain Backup Key provided the technical foundation that made this project possible. Read and excellent write-up on the problem this tool addresses by visiting their blog here: The downfall of DPAPI’s top-secret weapon